...
At the same time, we continue to get 0-day security risks for Flash.
This is not a zero-day exploit.
...
At the same time, we continue to get 0-day security risks for Flash.
...
At the same time, we continue to get 0-day security risks for Flash.
This is not a zero-day exploit.
Adobe releases emergency Flash fixes for two zero-day bugs
[...]
As part of that schedule, Adobe was to ship a Flash Player update next Tuesday, but it instead released the fixes early. In a Thursday advisory, Adobe confirmed that the update patched two vulnerabilities, designated CVE-2013-0633 and CVE-2013-0634. Not surprisingly, it rated the update critical: Criminals have been exploiting both vulnerabilities for an undisclosed amount of time.
"Adobe is aware of reports that CVE-2013-0633 is being exploited in the wild in targeted attacks designed to trick the user into opening a Microsoft Word document delivered as an email attachment which contains malicious Flash content," stated the advisory.
The second vulnerability, CVE-2013-0634, has been used in a similar fashion against Windows targets, but has also been exploited during "drive-by" attacks against Firefox and Safari users on the Mac, said Adobe. A drive-by attack requires only that a victim be duped into browsing to a malicious website hosting an exploit.
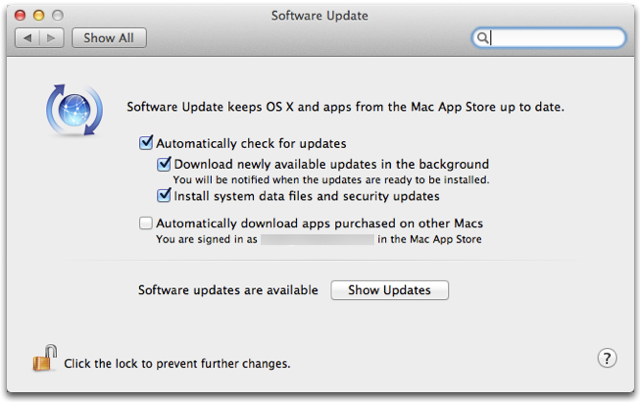
What I don't like is the ambiguity of the notification. Apple should know better. I get a random popup telling me that I need to update my Flash plain, yet when I go to Flash Player in sys prefs, it says Flash is up to date. It also doesn't help that Apple took away the icon in Safari that showed if the site had been verified or not.
Plenty of sites rely on flash to run, no flash no access.Flash, Flash, why do you crash?
Excuse me. I am one of the administrators (though not of as many systems as that) of a network which is mixed Mac/Windows network. Apple's enterprise system management leaves MUCH to be desired especially in a mixed environment. It is much easier and more trivial to push out a group policy than one of these commands. It would help if Apple's AD integration worked halfway decently.
...
We don't want to be cleaning up computers, but we also don't want apple flipping a switch and instantly rendering the tools that we use on a day to day basis instantly inoperable indefinitely while there is no update available to patch the hole. Users (at least the ones that work for us) are far more irritated when the whole organization can't do their day to day job than individual isolated computers being compromised.
Disabling third party software such as Java is not increasing security. It's called crippling someone else's system.
I say again: suppose a company uses a java based tool. Apple flips a switch and makes it useless. What would you tell them?
WTF doesn't Apple just give a warning and make the user DECIDE whether to disable it or not rather than just go around shutting down computers willy nilly without the users' permission? This strikes me as an invasion of privacy and frankly as pointed out with Java, it can do more damage than an actual threat in some cases if there's no update to move to (as was the case with Java at one point).
This Xprotect blocking is a PURE NIGHTMARE for enterprise users. I manage over 60 macs and updating each one by hand is such a PITA...
Can't it just be turned off then? There are other solutions if it is causing this much of an issue.
Plenty of sites rely on flash to run, no flash no access.
Apple never shuts down your Mac remotely, and when they issue an urgent security update like this, it doesn't secretly collect any private information from you.
If a user doesn't know how to use a different browser, and doesn't know how
to uncheck a box in Security preferences, then they aren't going to know how answer that question you think should be asked. They are not the expert able to judge the magnitude of the threat, and getting malware is almost NEVER going to be better than losing access to some app temporarily until you get tech support to install a workaround (or until an automatic patch comes along--in this case, instantly).
Leaving that kind of highly technical research and decision to a user who doesn't even understand the basic factors is asking for trouble on a scale
Windows knows all about.... The choice you want from Apple IS there, but it's for knowledgeable users, not thrown in the face of people who won't know what to do with it.
The problem is not Apple, it's Flash and Java being insecure--people ought to write to THEM saying how vital Flash and Java are, and demanding better security. Security is a feature just as vital--and to a LOT more people--than browser-based Java or Flash.
The complaints that Apple is "taking over" machines is nonsense. Anyone with admin privileges on a Mac can turn off this mechanism in their security settings. Apple has provided a great mechanism to secure their computers, they are actively using it, and they even provide a simple means for those not wanting to use it to turn it off. None of the complainers here show understanding of how that mechanism works.
If Apple hadn't drawn that line in the sand with the iPhone back in 2007, imagine how much worse the malware problem would be today.
I never hear any problems with Microsoft Silverlight. Is it extremely secure or just nobody uses it or cares?
That doesn't really make a lot of sense: you make it sound as if these sites are cast in concrete and cannot change. There are already hundreds of millions of computers that can't run Flash in their browser; what are those sites doing to run on those computers?
Zero-day Flash/Java exploits are coming at alarming frequency. Any website owner still relying on Flash to deliver their content needs to have their head examined.
I think you are hanging on the literal words "shut down" rather than what was implied (i.e. them throwing a switch to prevent you from running something you may want to run).
Who actually got any flipping Malware?
but it's an absolute CERTAINTY that your computer will be blocked from running things you may want to run when Apple puts something on their list [SNIP]
there's a huge difference between wanting to be warned about "downloads" and just out and out blocking a major part of the computer's capability (whether Flash or Java).
Dictators and the like [SNIP]
Flash and Java are legit apps with vulnerabilities that present a certain risk level, not malware themselves; OSX is the same way.
It can have a known vulnerability. Should Apple shut down all Macs until they can update OSX?
Do you have ANY idea how many vulnerabilities have been found in OSX and Windows over the years? You act like this issue is something related only to Java and Flash.
As I said to the other person above, turning off the safe download function AFTER it's disabled something like Java or Flash won't do you any good without going in and removing the program in question off the Plist and there is not user GUI access to that list so you'll have to manually edit it.
Besides, exactly who wants to DISABLE *ALL* security updates just to avoid having Apple turn off Flash or Java with no option to even temporarily re-enable them without jumping through hoops?
In other words, there's a BIG difference between a known trojan or worm and a vulnerability/exploit in something like Java.
The former should always be on EVERYONE's list and NEVER removed from it while the latter is blocking something legit from running that has some risk attached to it (e.g. playing Scrabble on Pogo.com doesn't really quality as much of a "risk" to approve Java to run anyway despite the exploit.
Yes, because Android smart phones are just rampant with people getting their stuff stolen because Flash is available for it.
I'm not saying they can't change I'm just saying what they are now using, it's like cars mostly run on petrol (Gasoline for those in the US) but there are also some that run of diesel it doesn't mean the manufactures are going to all switch to bio-fuels because it is better for the environment.
Your messages in this discussion have been ambiguous. Who is the "you" you're talking about? Who has been disenfranchised? I'm confident that MagnusVonMagnum knows how to hack plists, so it clearly wasn't you. In other words, the "you" you keep referencing is some hypothetical person...
Neither you nor Aiden seem to have carefully read the article you're commenting on.
Firefox or Safari on the Macintosh platform[/B][/I]. I'm taking Adobe's report at face value: this is a real zero-day attack. Do you have some reason to disagree?
Again, the "your" is referring to some hypothetical user who you assume has been disenfranchised, and you think you're qualified to speak for this hypothetical person.
Oh, please. Dictators don't give people an option of overriding the check, and they don't provide plists for people to manually edit. Do we really need to invoke Godwin's Law in this discussion?
Apple clearly disagrees, and I think Apple is completely right in their comprehensive response to this clear and present malware attack.
Please explain why your hypothetical about an OS X problem is remotely comparable to what happened this last week. Note: please actually read the Adobe security advisory before responding.
Why do you think the ancient history of malware pertinent in this discussion? What's pertinent is the malware threats present today.
Again, the "you" in that spaghetti-statement clearly isn't you. For some quaint reason, you presume to speak for some hypothetical disenfranchised person with hypothetical outrage over some hypothetical "dictator".
Nonsense. The only thing anyone had to do was to update Flash to the current version.
I'm not commenting on a specific article or this one specific incident
Who actually got any flipping Malware???
And who are YOU qualified to speak for?
Trying to run Flash-free for the past 4 months. So hard to quit I thought I would relapse. At times only when Safari for iOS is detected will the website display its available non-Flash version.Does anybody use flash anymore ? I been blocking flash for 4 years
BothI never hear any problems with Microsoft Silverlight. Is it extremely secure or just nobody uses it or cares?
Couldn't state it more clearly.(...)
No, people need to stop making users "do actual work" using poor platform choices and insecure software. Flash and Java's times are over. I'm glad Apple is doing this, because it highlights the fact that these plugins need to go.
I would take something to substantiate it with, not that I disagree, far from it.(...)
Really? iOS devices are far more secure than Android ones. Do you disagree?
That's the quintessence of a zero-day attack -- two zero-day attacks.
Neither you nor Aiden seem to have carefully read the article you're commenting on.
Ubuntu and Mac OS X user means sacrilege both to Mac and GNU/Linux communities.
There are no known zero-day attacks, on any platform.
Adobe is also aware of reports that CVE-2013-0634 is being exploited in the wild in attacks delivered via malicious Flash (SWF) content hosted on websites that target Flash Player in Firefox or Safari on the Macintosh platform, as well as attacks designed to trick Windows users into opening a Microsoft Word document delivered as an email attachment which contains malicious Flash (SWF) content.
You claim to carefully read, but you don't understand what you are reading.
Aiden, it's sort of a bizarre thing to say without explaining your claim.
"A zero-day (or zero-hour or day zero) attack or threat is an attack that exploits a previously unknown vulnerability in a computer application, meaning that the attack occurs on "day zero" of awareness of the vulnerability.[1] This means that the developers have had zero days to address and patch the vulnerability. Zero-day exploits (actual software that uses a security hole to carry out an attack) are used or shared by attackers before the developer of the target software knows about the vulnerability."
http://en.wikipedia.org/wiki/Zero-Day_Attack
Making the one-line claim without explaining yourself contributes nothing to the discussion.
The Adobe security bulletin was quite explicit: CVE-2013-0634 is being exploited in the wild in attacks delivered via malicious Flash (SWF) content hosted on websites that target Flash Player in Firefox or Safari on the Macintosh platform. I am also baffled why Adian said that this wasn't a zero-day attack. The attacks are really happening, and real people are being harmed.
OTOH, you are not being wronged with Apple's anti-malware efforts. You are clearly clever enough to hack the plists if you needed to do that. You're complaining on behalf of some hypothetical user. I've gotta ask: why don't you just let those [hypothetically wronged] users speak for themselves?
Bingo. That's the exact question you need to ask yourself, Magnus. If some real user was harmed by Apple's system, they should speak for themselves. You were clearly not harmed.
Once the exploit is known, it is no longer zero-day. This exploit is not only known, but a patch is available. It is not a zero-day attack.
One can always hope that it would trigger someone into looking up the definition of the term, and realize that it was being mis-used.
This is not a zero-day exploit.
Can you point to a single place where any credible reporter or security expert is using your particular definition of "zero-day attack"? AFAICT, yours is an obfuscation that no credible reporter or security expert is making. Claiming that CVE-2013-0634 isn't a zero-day attack is doing a disservice both to the term and to the discussion here.
...
and I see this isn't the only time you've attempted to impose your personal definition of "zero-day" into a MR discussion. Unless you can produce some credible source that actually backs up what you say, I request you stop doing this.
The wikipedia article you reference certainly doesn't say it. If you tried to add such nonsense to the wikipedia page, it would be removed.
"A zero-day (or zero-hour or day zero) attack or threat is an attack that exploits a previously unknown vulnerability in a computer application, meaning that the attack occurs on "day zero" of awareness of the vulnerability.[1] This means that the developers have had zero days to address and patch the vulnerability. Zero-day exploits (actual software that uses a security hole to carry out an attack) are used or shared by attackers before the developer of the target software knows about the vulnerability."
http://en.wikipedia.org/wiki/Zero-Day_Attack
Can you point to a single place where any credible reporter or security expert is using your particular definition of "zero-day attack"? AFAICT, yours is an obfuscation that no credible reporter or security expert is making. Claiming that CVE-2013-0634 isn't a zero-day attack is doing a disservice both to the term and to the discussion here.
Can you produce any evidence to support the claim that an exploit for which a patch is already available is still a "zero-day exploit".
I don't need to "add nonsense" to the Wikipedia article - it's already in 100% agreement with what I am saying.
How on earth can you continue to blather on about calling a known attack with an available patch a "zero-day" exploit?
By definition, labeling the exploit "CVE-2013-0634" removes it from the "zero-day" category, and places it into the "known" category.

