Become a MacRumors Supporter for $50/year with no ads, ability to filter front page stories, and private forums.
600,000 Macs Worldwide Reportedly Infected by Flashback Trojan
- Thread starter MacRumors
- Start date
- Sort by reaction score
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
thank you for posting this...
JOY!
My iMac is completely clean which is more than I can say about my mind...

Thanks so much for posting these...
----------
until I pasted both of those commands separately and pressed return after entering each command.
Both came up that does not exist when I did it this way.
Hope that helps
clean here, update your system often and you should not run into this trojans...
The malware self-installs after you visit a compromised or malicious webpage. Obviously, it would be a good idea to update any Macs in your control.
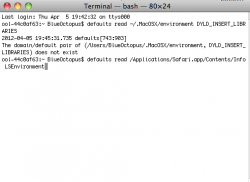
For those who want to check if mac is infected (from F-Secure instructions):
Run the following command in terminal:
defaults read /Applications/Safari.app/Contents/Info LSEnvironment
defaults read ~/.MacOSX/environment DYLD_INSERT_LIBRARIES
If you get "The domain/default pair ... does not exist" for both - you are clean
from 9to5mac
JOY!
My iMac is completely clean which is more than I can say about my mind...
Thanks so much for posting these...
----------
Guys I'm not goetting the does not exist for the first command entering into Terminal - Or am I reading it wrong?
until I pasted both of those commands separately and pressed return after entering each command.
Both came up that does not exist when I did it this way.
Hope that helps
The news reports are claiming 600,000 Mac infected. If that is true, then I would expect at least a few MacRumors forum readers would be infected. Anyone who found a Flashback infection please speak up.
I dispute this figure and the keyword that makes all those warning signs go off in my gut is "RUSSIAN" and appears to me to be a scare tactic to get people to buy antivirus. Now where was that last company from that may have been doing battle with Apple's security updates awhile back and weren't they promoting AV software. Funny how once they were raided Apple won the battle. Could this just be another tactic?
I got a Flash (Java) popup today, but I did not install it and closed out immediately. I also have not found Flashback on my computer, but I don't really know where to look.
OK just got home from work and copied and pasted the commands in terminal. CLEAN! Woo hoo! I suspected I would be ok since I do not even have java installed but I wanted to be sure. Thanks everyone for the tips and op for the link!

JOY!
My iMac is completely clean which is more than I can say about my mind...
Thanks so much for posting these...
----------
until I pasted both of those commands separately and pressed return after entering each command.
Both came up that does not exist when I did it this way.
Hope that helps
And here we go! Thanks for sharing, checking now...
That makes very little, if any, difference. Running a standard account vs an admin account doesn't ensure security.
Nothing like making a statement that goes against well-established computer security practice without bothering to provide even anecdotal evidence in support for your statement...
Using an account that operates at the lowest necessary privilege level is Security 101. Heck, it's remedial - more like Security 097.
This is the standard Unix security model, and it works very well. Microsoft has finally followed suit, to the benefit of their users. Mac makes it very easy to do as well - unfortunately a lot of Mac users still don't think about security because they haven't been caught with their pants down. Yet. They get a little scared when these stories come out; they check to make sure their system is clean... and then they forget all about security, until the next scary story hits.
Well, according to Apple, the number of unique OS X installs in 2009 was 75 million. Over the last 3 years, Apple has averaged Mac sales of 5 million per quarter, so that leaves a potential maximum of 135 million Macs. Let's say that in every year since 2009, 10% of the existing Macs were retired, that would reduce the total number of Macs in service by 20 million. So let's say that there are 115 Macs currently in use worldwide. 0.6 million/115 million * 100% = 0.5%Percentage wise - are more Mac computers now infected with malware than their Windows 7 counterparts?
Microsoft has publicly stated that infection rates for Windows 7 were 0.4% one year ago, but they were increasing by 33% year over year. So it would appear that if this claim is correct, and if Microsoft is correctly reporting infection rates, then assuming that year-over-year increases in infection rates of Windows 7 installations remained constant, then infection rates of OS X and Windows 7 would be quite comparable.
This may help you understand. There have been other more technically detailed explanations posted over the years, which you can find by searching, if you wish.Nothing like making a statement that goes against well-established computer security practice without bothering to provide even anecdotal evidence in support for your statement.
Well, according to Apple, the number of unique OS X installs in 2009 was 75 million. Over the last 3 years, Apple has averaged Mac sales of 5 million per quarter, so that leaves a potential maximum of 135 million Macs. Let's say that in every year since 2009, 10% of the existing Macs were retired, that would reduce the total number of Macs in service by 20 million. So let's say that there are 115 Macs currently in use worldwide. 0.6 million/115 million * 100% = 0.5%
Microsoft has publicly stated that infection rates for Windows 7 were 0.4% one year ago, but they were increasing by 33% year over year. So it would appear that if this claim is correct, and if Microsoft is correctly reporting infection rates, then assuming that year-over-year increases in infection rates of Windows 7 installations remained constant, then infection rates of OS X and Windows 7 would be quite comparable.
Your math only holds if this is the only trojan affecting Macs. The infection rate for Win 7 is for all malware.
Guys I'm not goetting the does not exist for the first command entering into Terminal - Or am I reading it wrong?
If I run them individ. no messages past the code shows up only when i run them together.
Please read the thread. Macs have never been virus-proof and this isn't a virus.We all knew this would happen some day. Macs are no longer virus proof.
If I run them individ. no messages past the code shows up only when i run them together.
Post #252 answered you. I think.
You need to run them individually. Your screenshot showed the correct response for uninfected, but only on one of the two commands. In your screenshot it appears you didn't hit enter after pasting the other. Both of the commands that start with 'defaults' need to have enter pressed after they are pasted - looks like you only did that after 1 of them.
Except that if this number is true, then this particular trojan would represent 99.9% of all known Mac malware.Your math only holds if this is the only trojan affecting Macs. The infection rate for Win 7 is for all malware.
Personally, given that the number is almost identical to the published rate for Windows 7 infections, I suspect that the number of infected machines was just estimated based on this previously published statistic. There is absolutely no reason to believe that the site that published these numbers has any evidence to back them up.
Probably the biggest question regarding the credibility of Dr. Web on this issue is why they didn't disable the botnet when they sinkholed it. This is a serious question to be asked of security companies, because sinkholing a botnet just redirects the illegally incoming information to the security company's server. The more credible security companies use sinkholing to disable botnets, but their less ethical counterparts use these means for financial gain by selling/monetizing the information obtained by the sinkhole.
Last edited:
Post #252 answered you. I think.
You need to run them individually. Your screenshot showed the correct response for uninfected, but only on one of the two commands. In your screenshot it appears you didn't hit enter after pasting the other. Both of the commands that start with 'defaults' need to have enter pressed after they are pasted - looks like you only did that after 1 of them.
Yes thanks SNG I just didn't press enter like a shmuck. I am clear - thanks!
ok, so i ran the terminal commands and came up clean, but just noticed that ClamXAV just found jsched / OSX.Flashback 8 and it's still scanning. this was also after i skipped a CLAM update that featured the option to disregard "infected" files for future scans. WTF! what exactly does this virus do to your machine if it's been on my macbook?
ok, so i ran the terminal commands and came up clean, but just noticed that ClamXAV just found jsched / OSX.Flashback 8 and it's still scanning. this was also after i skipped a CLAM update that featured the option to disregard "infected" files for future scans. WTF! what exactly does this virus do to your machine if it's been on my macbook?
That is interesting. I don't know the answer to that though. Not many (in the big scheme of things) got infected, and even less post on forums, so you might be breaking new ground here. Perhaps someone better informed than I can chime in.
If I had to make a crude, off the cuff, guess. Then I would say that ClamAV quarantined your infection a few days ago. So it has effectively removed it from your system (which is why the terminal stuff shows you are clean). But ClamAV still knows, and is holding, your infection, so it reports that you still 'have it'.
//My guess is based on having a Windows AV 'quarantine' a virus (or suspected one). And how it deals with them. I have no first hand experience with an AV in OS X.
I think the initial package scans for ClamXav and aborts the installation of the full package if the antivirus software is present, so you probably don't have a full/active installation. Just follow the ClamXav recommendations once it finishes its scan.ok, so i ran the terminal commands and came up clean, but just noticed that ClamXAV just found jsched / OSX.Flashback 8 and it's still scanning. this was also after i skipped a CLAM update that featured the option to disregard "infected" files for future scans. WTF! what exactly does this virus do to your machine if it's been on my macbook?
Let us know what happens with this, because you are the first person I've seen posting to say they have evidence of an infection. You'd think that if more than 600,000 Macs were affected, that at least some people on these forums would be affected.
Having Dr. Web sinkhole the botnet, IMO, is better than having criminals. The question is how would Dr. Web disable the botnets? Should they issue a command so that the trojan deletes itself? Does this violate any (local and international) laws? Is it in Dr. Web's right to delete files from my computer without my authorization even though it's for my best interest? Will Dr. Web be held liable if they damage the computer while trying to disable it?Except that if this number is true, then this particular trojan would represent 99.9% of all known Mac malware.
Personally, given that the number is almost identical to the published rate for Windows 7 infections, I suspect that the number of infected machines was just estimated based on this previously published statistic. There is absolutely no reason to believe that the site that published these numbers has any evidence to back them up.
Probably the biggest question regarding the credibility of Dr. Web on this issue is why they didn't disable the botnet when they sinkholed it. This is a serious question to be asked of security companies, because sinkholing a botnet just redirects the illegally incoming information to the security company's server. The more credible security companies use sinkholing to disable botnets, but their less ethical counterparts use these means for financial gain by selling/monetizing the information obtained by the sinkhole.
I think Dr. Web best option is to notify the ISP and let the ISP notify their customers, but this is a time consuming process and potentially costly for both Dr. Web and the ISPs.
That is interesting. I don't know the answer to that though. Not many (in the big scheme of things) got infected, and even less post on forums, so you might be breaking new ground here. Perhaps someone better informed than I can chime in.
If I had to make a crude, off the cuff, guess. Then I would say that ClamAV quarantined your infection a few days ago. So it has effectively removed it from your system (which is why the terminal stuff shows you are clean). But ClamAV still knows, and is holding, your infection, so it reports that you still 'have it'.
//My guess is based on having a Windows AV 'quarantine' a virus (or suspected one). And how it deals with them. I have no first hand experience with an AV in OS X.
update:
i had no quarantine folder established so i re-ran it, directing it to send it to a folder on my desktop and then i deleted it. i am re-scanning now. it had been a few weeks since i ran Clam before tonight; i figured i was in the clear after running the terminal commands and was shocked to see Clam immediately find it in its scan (it was found within seconds of the clam scan when i first checked tonight).
before i deleted the folder i scanned the desktop with Clam and it saw it there, i couldn't actually see the file in the folder but deleting the folder and rescanning seems to turning up clean (it's past the point where it first found it)
----------
PS - i know i was a rare report of an infection, but i don't know if any of the people who figured they were "clean" after running terminal checked a Clam scan yet.. i bet if everyone was running ClamXAV you'd be seeing more reports. i'm pretty careful with what i click on/authenticate so i'm pretty shocked to have even seen it at all on my setup (even if the existence of CLAM on my macbook may have blocked it from actually installing itself).
oleus - in my experience dealing with windows infections and AV, that seems normal. I think if you can make your AV say the system is clean, and you can pass F-Secure's method of being clean, then you are clean.
I know it is a dirty feeling, knowing that you had something, but if 2 different things say you are clean and you aren't otherwise getting any odd behavior, you should be good to go.
I know it is a dirty feeling, knowing that you had something, but if 2 different things say you are clean and you aren't otherwise getting any odd behavior, you should be good to go.
This is how you take down a botnet with a sinkhole.Having Dr. Web sinkhole the botnet, IMO, is better than having criminals. The question is how would Dr. Web disable the botnets? Should they issue a command so that the trojan deletes itself? Does this violate any (local and international) laws? Is it in Dr. Web's right to delete files from my computer without my authorization even though it's for my best interest? Will Dr. Web be held liable if they damage the computer while trying to disable it?
I think Dr. Web best option is to notify the ISP and let the ISP notify their customers, but this is a time consuming process and potentially costly for both Dr. Web and the ISPs.
oleus - in my experience dealing with windows infections and AV, that seems normal. I think if you can make your AV say the system is clean, and you can pass F-Secure's method of being clean, then you are clean.
I know it is a dirty feeling, knowing that you had something, but if 2 different things say you are clean and you aren't otherwise getting any odd behavior, you should be good to go.
then i feel clean
i still don't fully understand what this virus "does" when fully implemented on a machine. so i don't even know what i was possibly at risk of. what's the point of this virus, i guess is what i am asking. i have read 4 articles and i still don't have that answer.
Register on MacRumors! This sidebar will go away, and you'll see fewer ads.