I wanted to follow-up on this because as it turns out Filevault2 only protects the user when the hard disk not mounted, i.e. the laptop is powered off.
When I log in to my MBA, I first give the password to decrypt the machine. I am then taken to the user login screen to give the password for whichever user I want to sign in to the machine. The machine boots.
When I wake the computer from sleep mode, I am only required to give the user password to unlock the OS, there is no requirement to unlock the filesystem because the encryption keys are cached and thus stored in memory. In order to encrypt your drive you must power down the laptop completely.
For most people, the OS password is sufficient when their laptop is in the house or in their possession, but the user should always be aware that when you put your system into sleep mode (close the lid on the MBA), the hard drive is NOT protected with FileVault.
For maximum security, you must power down your system to ensure the hard drive dismounts.
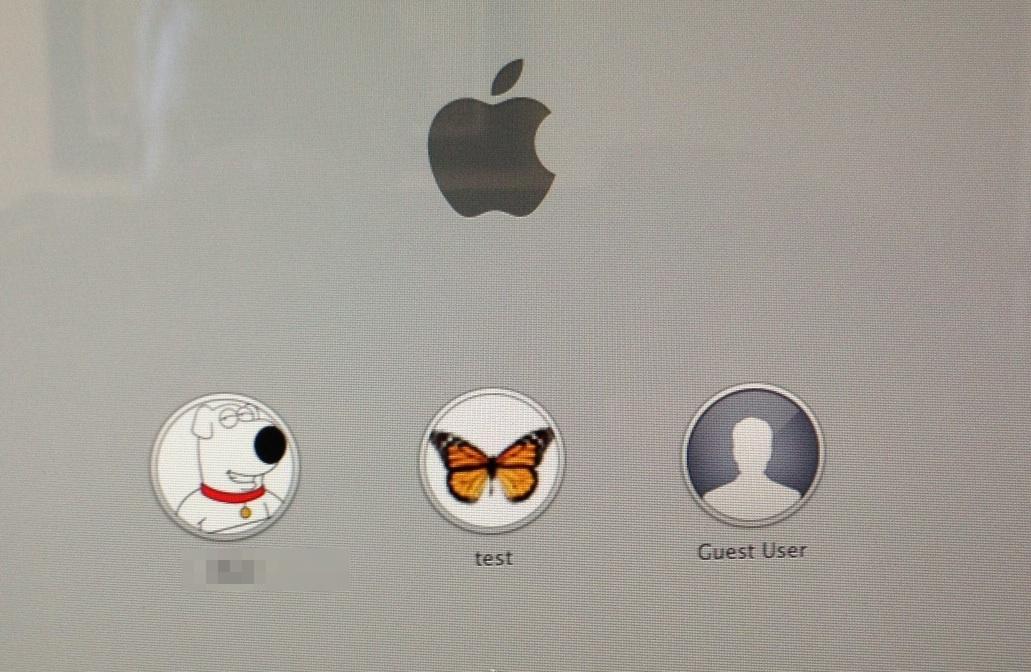
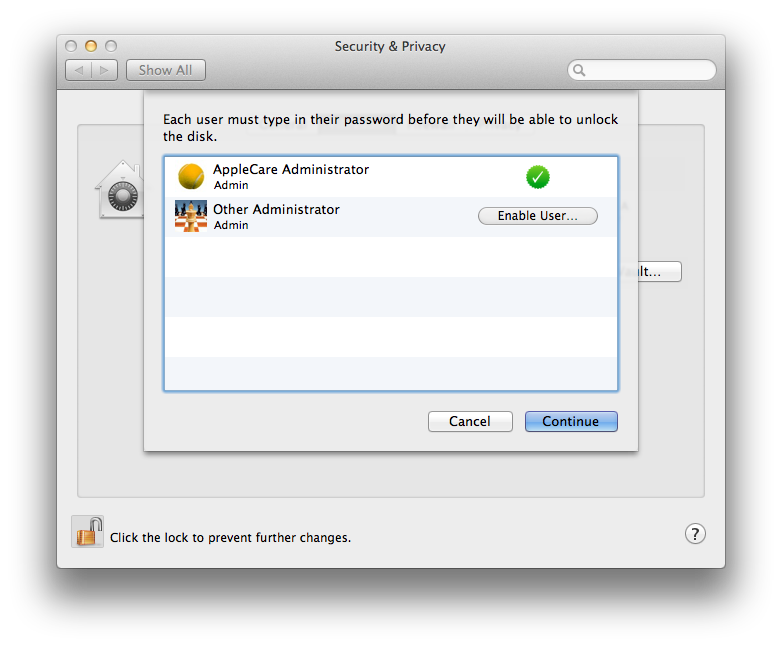
I'm not sure what you mean by two passwords? When you boot a system with FV2, it boots from the Recovery HD partition (FV2 is still locked) and presents the screen below with user accounts. For example, in the screen below if I click the test account and enter the PW it logs in and at the same times opens the FV2 image and allows access. There is no second password.
You are correct that the FV2 is open unless you shutdown, but the system is still protected by your user password, which is the
same password used to open the FV2 encryption anyway. So if you have a strong PW, the system is just as safe either way. Theoretically, yes, I suppose it would be better to shutdown... but as a practical matter there is currently no way to get past the PW either way.
There is no way to grab the PW from the system, even though it is logged on. There was a away to do this via "direct memory access" (DMA) over Firewire/Thunderbolt, but that was blocked with Lion 10.7.2.
----------
I don't see how an EFI password really "helps" anything to protect the hard drive. If the attacker wants to get to the data on your hard drive then can always remove the drive from the computer and get to the data directly. No EFI password needed.
It helps because with Lion and Mountain Lion the admin password can be reset by booting to the Recovery HD, and having EFI locked stops that. It will also stop a "maid in the middle" attack from setting up an alternate boot drive to snag your password. Like you said, neither would crack FV2, but it would at least make the thieving weasels have to remove the drive before that even tried any hacks.