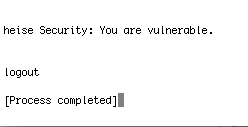
According to The Register, a large vulnerability has been found in Leopard's mail.app allowing attackers to run malicious code on a victim's machine by disguising an executable program as an image or other type of innocuous file.
It uses a security hole that was fixed in OSX 10.4 Tiger in March 2006, but seems to have been re-opened in OSX 10.5 Leopard.
There is a demo of how the bug works at Heise Security.
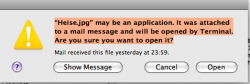
It works by the attacker sending you an email with an attachment that claims to be a safe file eg a .jpg, but is actually an executable program. A user can become infected simply by clicking on an attachment that looks like a jpeg image.
A patched version of Tiger will flag up this kind of file as possibly unsafe. Leopard does not, and will run it automatically.
Register article
It uses a security hole that was fixed in OSX 10.4 Tiger in March 2006, but seems to have been re-opened in OSX 10.5 Leopard.
There is a demo of how the bug works at Heise Security.
It works by the attacker sending you an email with an attachment that claims to be a safe file eg a .jpg, but is actually an executable program. A user can become infected simply by clicking on an attachment that looks like a jpeg image.
A patched version of Tiger will flag up this kind of file as possibly unsafe. Leopard does not, and will run it automatically.
Register article