23-April-2015-13:55 EST
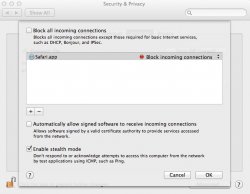
I have noticed this issue on Yosemite as well as Mountain Lion. When I have "Blocked all incoming connections" not checked and I add Safari to the fire wall with "Block incoming connections" Safari is still able to communicate with the internet.
This appears to be a fault as no communications should occur for Safari? See enclosed. I have also posted this in the Apple forum under the name "Firewall Problem"
I have noticed this issue on Yosemite as well as Mountain Lion. When I have "Blocked all incoming connections" not checked and I add Safari to the fire wall with "Block incoming connections" Safari is still able to communicate with the internet.
This appears to be a fault as no communications should occur for Safari? See enclosed. I have also posted this in the Apple forum under the name "Firewall Problem"