
The company did not divulge specific details on how hackers accessed the iCloud accounts, leading Wired writer Andy Greenberg to investigate the methods that hackers might possibly have used to acquire the stolen media.
Greenberg visited Anon-IB, a popular anonymous image board where some of the celebrity photos first originated, and discovered that hackers openly discuss exploiting software designed for law enforcement and government officials. Called ElcomSoft Phone Password Breaker (EPPB), the software in question lets hackers enter a stolen username and password to obtain a victim's full iPhone/iPad backup.
Acquiring just a user name and password allows hackers access to content on iCloud.com, but with the accompaniment of the ElcomSoft software, a complete backup can reportedly be downloaded into easy-to-access folders filled with the device's contents."Use the script to hack her passwd...use eppb to download the backup," wrote one anonymous user on Anon-IB explaining the process to a less-experienced hacker. "Post your wins here ;-)"
According to security researcher Jonathan Zdziarski, who spoke to Wired, metadata from some of the leaked photos is in line with the use of the ElcomSoft software and possibly the iBrute software, which exploited a vulnerability in Find My iPhone to allow hackers unlimited attempts to guess a password. Apple has, however, patched the exploit, and has suggested iBrute was not a factor in the attacks.
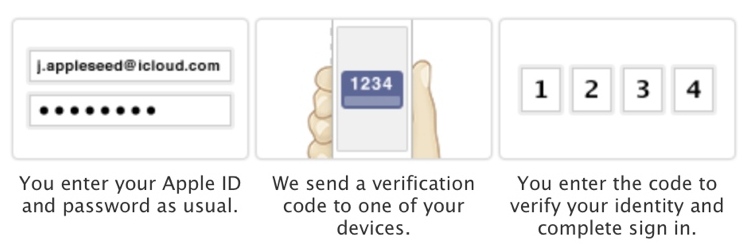
As noted by TechCrunch, using ElcomSoft's software to download an iPhone's backup successfully circumvents two-factor verification as the two-factor authentication system does not cover iCloud backups or Photo Stream.
Two-factor verification can make it much more difficult for hackers to acquire a user's login credentials in the first place, preventing many attacks, but an iCloud backup can be installed with just a user name and a password.
The ElcomSoft software does not require any credentials to buy and while it costs $399, it is also available on bittorrent sites. The vulnerability in iCloud backups has been known for some time, with ElcomSoft's own CEO pointing towards the lack of two-factor authentication for iCloud backups back in May of 2013.
Apple has explored expanding two-factor authentication to some iCloud services, but an official expansion of the security feature has not yet been introduced.
Article Link: Hackers Using Law Enforcement Tools to Access iCloud Backups Unprotected by Two-Factor Authentication





