Got a tip for us?
Let us know
Become a MacRumors Supporter for $50/year with no ads, ability to filter front page stories, and private forums.
'Huge' Number of Mac Apps Open to Hijacking From Sparkle Updater Vulnerability
- Thread starter MacRumors
- Start date
- Sort by reaction score
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Trim Enabler has now been updated (3.4.3) with a fix. Make sure to update using a secure/trusted internet connection, or redownload from https://www.cindori.org/software/trimenabler/
If you take a look at this page: https://www.taoeffect.com/blog/2016...falling-protecting-yourself-from-sparklegate/
one of the ways to prevent the attack is to have run Firefox once. Hopefully that means I'm safe.
So according to this article, it's a flaw in OS X, not Sparkle directly? But if you have Firefox on your machine and have run it at least once, you are safe?
-Kevin
Right, I use nightly build. 2.84 (14306) Thank you. Works fine though. Tick "Include beta releases" at the bottom to get it.
This does not work. Apparently they don’t have a beta release at the moment. They just have the stable release and the developer nightly builds. You should download them here: https://build.transmissionbt.com/job/trunk-mac/.
But if you have Firefox on your machine and have run it at least once, you are safe?
No, that is not true and it follows from the article also. When Firefox is installed, then the FTP protocol will be handled with Firefox instead of Finder. However, other protocols can be used too, so this is not a fix.
The problem is that Sparkle has a web view in one of its panels that is used to show patch notes and changes. The content of that web view can come from a remote URL that is specified in the feed URL. When that remote URL is changed into something else other than a static web page, like an FTP address, then this can be exploited due to a bug in the web view (which is a WebKit component) and Finder (because it is the default FTP/AFP/SMB handler). An exploit could load a program or script via one of these protocols that is then executed.
Last edited:
Interesting. The Apple technician had me shift-click on Safari, which allowed it to open normally. Then ironically she had me download Malwarebytes -- which is one of the currently affected pieces of software!
Well we could be talking about different things but your scenario sounded awfully close to what I noticed on that website I use. And that is just a gimmick taking advantage of Safaris popup handling and cleverly disguising itself.
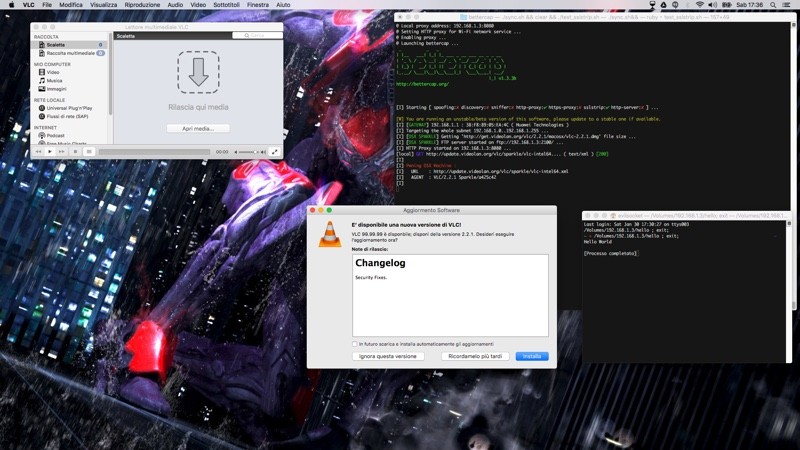
This is what I get when I run the code suggested by KALLT
http://www.fremacsoft.net/appcleaner/Updatrs.xml
http://audirvana.com/delivery/audirvanaplus_appcast.xml
http://update.videolan.org/vlc/sparkle/vic-intel64.xml
I'v already updated VLC so hopefully no more issues (you'd think). Just to understand, if I disable auto update and update via the website this would avoid the problem??
http://www.fremacsoft.net/appcleaner/Updatrs.xml
http://audirvana.com/delivery/audirvanaplus_appcast.xml
http://update.videolan.org/vlc/sparkle/vic-intel64.xml
I'v already updated VLC so hopefully no more issues (you'd think). Just to understand, if I disable auto update and update via the website this would avoid the problem??
Mac app isn't part of iOS and OS X ?This does not solve the problem.
[doublepost=1455096373][/doublepost]
This is has nothing to do with OS X.
[doublepost=1455096650][/doublepost]
No risk in real life situations.
[doublepost=1455128020][/doublepost]
Yeah back in sl says... But now it appears OS X is the new disabled kid. And yeah it's not vulnerable to OS X itself but Mac app is part of OS xNo, the App Store - at least not in the way that Apple implemented it - is NOT a good thing, for a rather long list of reasons. The App Store (and its lack of support for paid updates and upgrades) is not only an economic problem for software developers, it also did not prevent several malware from being distributed through it. Just Google for something like "apple app store malware" and you will find plenty of articles about it.
That being said, nothing is perfect, but I'd rather live with an occasional security issue with Sparkle and other installers/update tools than with a system where the monopolistic App Store would be the only means of obtaining and installing software.
[doublepost=1455113354][/doublepost]
It never was safe. There only was a time when its market share was so insignificant that nobody bothered exploiting its vulnerabilities. That time is gone and now people wake up to the reality that they bought into hype and marketing -- and that Apple's platform is by no means safer than Microsoft's. However, just to get this straight, a vulnerability is Sparkle is not a vulnerability in OS X itself.
Thank you KALLT.This does not work. Apparently they don’t have a beta release at the moment. They just have the stable release and the developer nightly builds. You should download them here: https://build.transmissionbt.com/job/trunk-mac/.
A Mac app isn't part of iOS.Mac app isn't part of iOS and OS X ?
[doublepost=1455128020][/doublepost]
Yeah back in sl says... But now it appears OS X is the new disabled kid. And yeah it's not vulnerable to OS X itself but Mac app is part of OS x
If anyone used it when it worked, Carrier Editor shows up in my search.
http://uhelios.com/downloads

http://uhelios.com/downloads
As I side note, I encountered my first piece of malware on my Mac. I have no idea how I got it, but Safari was frozen with a repeating string of pop-ups telling me I had malware installed. A quick call to Apple's tech support resolved it. But it caught me by surprise.
Wow, that's one more piece of malware than I've ever encountered on Windows.
A pair of vulnerabilities in the framework that some Mac apps use to receive automatic updates leaves them open to man-in-the-middle attacks, according to a report from Ars Technica covering a security flaw that was first discovered by a security researcher named Radek in late January.
Apps that use a vulnerable version of Sparkle and an unencrypted HTTP channel for server updates are at risk of being hijacked to transmit malicious code to end users. The Sparkle framework is used by apps outside of the Mac App Store to facilitate automatic software updates.
Some of the affected apps are widely downloaded titles like Camtasia, Duet Display, uTorrent, and Sketch. A proof of concept attack was shared by Simone Margaritelli using an older version of VLC, which was recently updated to patch the flaw. The vulnerabilities were tested on both OS X Yosemite and the most recent version of OS X El Capitan.
A "huge" number of apps are said to be at risk, but as Ars Technica points out, it is difficult to tell exactly which apps that use Sparkle are open to attack. GitHub users have compiled a list of apps that use Sparkle, but not all use the vulnerable version and not all transfer data over non-secured HTTP channels.
Apps downloaded through the Mac App Store are not affected as OS X's built in software update mechanism does not use Sparkle.
Sparkle has released a fix in the newest version of the Sparkle Updater, but it will take some time for Mac apps to implement the patched framework. Ars Technica recommends concerned users with potentially vulnerable apps installed avoid using unsecured Wi-Fi networks or do so only via a VPN.
Article Link: 'Huge' Number of Mac Apps Open to Hijacking From Sparkle Updater Vulnerability
Here is what you need to know what to do http://blog.devmate.com/post/139057591966/sparkle-vulnerability-issue-whos-in-danger-and
So even if I use a VPN, the update server might not use HTTPS, which would put me at risk?
A VPN is fine (unless you do not trust the service). The problem of this vulnerability is that a ‘man in the middle’ could get between your computer and the developer’s server and insert a fake feed that causes Sparkle to download something else, potentially malware. This is a risk with HTTP is general and HTTPS mitigates this because your system will not accept a connection if something is wrong with the HTTPS, e.g. if it has been tampered with by a man in the middle. Likewise, a VPN creates an encrypted connection between your device and your VPN provider and every connection, HTTP or HTTPS or otherwise, will be protected from man-in-the-middle attacks.
Realistically speaking, this vulnerability is really only an issue if you do not trust your Internet connection. For instance, if you do not control the router or access point, e.g. public Wi-Fi or an Internet cafe. At home, this is typically not an issue. A VPN is something you should use anyway when you are using someone else’s Internet connection.
That's good to know. I run my own Pritunl VPN 24/7 on a Linode VPS. I was just worried about the connection from my Linode to the update server, which I have no control over. Sounds like that might still be a problem, but I'm one step ahead just using a VPN.A VPN is fine (unless you do not trust the service). The problem of this vulnerability is that a ‘man in the middle’ could get between your computer and the developer’s server and insert a fake feed that causes Sparkle to download something else, potentially malware. This is a risk with HTTP is general and HTTPS mitigates this because your system will not accept a connection if something is wrong with the HTTPS, e.g. if it has been tampered with by a man in the middle. Likewise, a VPN creates an encrypted connection between your device and your VPN provider and every connection, HTTP or HTTPS or otherwise, will be protected from man-in-the-middle attacks.
Realistically speaking, this vulnerability is really only an issue if you do not trust your Internet connection. For instance, if you do not control the router or access point, e.g. public Wi-Fi or an Internet cafe. At home, this is typically not an issue. A VPN is something you should use anyway when you are using someone else’s Internet connection.
It is believed that your OS platform is secure, yet here's is another example of how third party soft puts your computer in a risk. This is developers' responsibility to assure their app security. I really like DevMate's vision of the situation, simple things like implemented HTTPS protocol and updating Sparkle to the latest fixed version do matter.
Trim Enabler has now been updated (3.4.3) with a fix. Make sure to update using a secure/trusted internet connection, or redownload from https://www.cindori.org/software/trimenabler/
Thank you for your immediate reaction!
Because if your software is free, as is the case with most of those apps, having to pay for the privilege of being on the Mac App Store is beyond ridiculous, when you can host it yourself on GitHub, or your own website or in a million other places.Any reason why more apps don't use the App Store?
I've asked Team Viewer, VLC and Skype to deliver via the App Store but as you can see, my requests were in vain.
And GitHub uses HTTPS for updates, so it’s as safe, or nearly as safe, as the Mac App Store.Because if your software is free, as is the case with most of those apps, having to pay for the privilege of being on the Mac App Store is beyond ridiculous, when you can host it yourself on GitHub, or your own website or in a million other places.
Sparkle has released a fix in the newest version of the Sparkle Updater, but it will take some time for Mac apps to implement the patched framework. Ars Technica recommends concerned users with potentially vulnerable apps installed avoid using unsecured Wi-Fi networks or do so only via a VPN.
Article Link: 'Huge' Number of Mac Apps Open to Hijacking From Sparkle Updater Vulnerability
Hi there!
TechSmith, the developers for Camtasia for Mac and Snagit for Mac, two of the many applications that had been affected by the Sparkle MITM vulnerability released an update on Tuesday, March 8th to both Camtasia and Snagit that addresses this vulnerability. For those that are running Camtasia or Snagit, to receive the update simply open the application and go to the Snagit or Camtasia menu and choose "Check for Updates" and it will begin the update process. For those that want to update manually, you can head to this link and select the appropriate application to receive the latest version.
Robert R.
Technical Support Specialist
TechSmith Corporation
Register on MacRumors! This sidebar will go away, and you'll see fewer ads.