

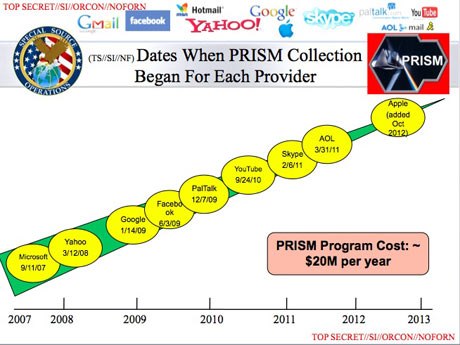
Apple reportedly joined the program in 2012, though Microsoft has been involved since 2007. It is unknown how or why Apple resisted joining the program for five years, nor why it decided to join in 2012. Twitter is noticeably absent from the list of companies, while Dropbox is said to be "coming soon".
Update: An Apple spokesperson gave this statement to AllThingsD:
Longtime Apple board member and former U.S. Vice President Al Gore tweeted earlier: "In digital era, privacy must be a priority. Is it just me, or is secret blanket surveillance obscenely outrageous?"We have never heard of PRISM. We do not provide any government agency with direct access to our servers, and any government agency requesting customer data must get a court order.
Data from the program, code-named PRISM, is frequently used in the President's Daily Brief -- a daily intelligence report for the U.S. President -- with PDB briefings citing PRISM data 1,477 times last year. The Post reports that data from PRISM accounts for nearly 1 in 7 intelligence reports.
From The Washington Post:
PRISM is an heir, in one sense, to a history of intelligence alliances with as many as 100 trusted U.S. companies since the 1970s. The NSA calls these Special Source Operations, and PRISM falls under that rubric.
The Silicon Valley operation works alongside a parallel program, code-named BLARNEY, that gathers up "metadata" -- address packets, device signatures and the like -- as it streams past choke points along the backbone of the Internet. BLARNEY's top-secret program summary, set down alongside a cartoon insignia of a shamrock and a leprechaun hat, describes it as "an ongoing collection program that leverages IC [intelligence community] and commercial partnerships to gain access and exploit foreign intelligence obtained from global networks."
Apple's privacy policy does make allowances for this sort of disclosure to the authorities:
The Washington Post and Guardian stories contain much more about PRISM, including slides from a PowerPoint presentation outlining the program that is classified TOP SECRET.It may be necessary - by law, legal process, litigation, and/or requests from public and governmental authorities within or outside your country of residence - for Apple to disclose your personal information. We may also disclose information about you if we determine that for purposes of national security, law enforcement, or other issues of public importance, disclosure is necessary or appropriate.
The Guardian reported earlier today that the National Security Agency is collecting call logs from Verizon Business Network Services "on an ongoing daily basis" on all calls "between the United States and abroad" or "wholly within the United States, including local telephone calls." The data includes "the numbers of both parties on a call [...], as is location data, call duration, unique identifiers, and the time and duration of all calls".
Update 7:41 PM: Director of National Intelligence James Clapper has issued a press release noting that the Washington Post and Guardian reports contain "numerous inaccuracies" and indicating that any data collection is limited to non-U.S. citizens located outside of the United States.
Note: Due to the political nature of the discussion regarding this topic, the comment thread is located in our Politics, Religion, Social Issues forum. All MacRumors forum members and site visitors are welcome to read and follow the thread, but posting is limited to forum members with at least 100 posts.Section 702 is a provision of FISA [the Foreign Intelligence Surveillance Act] that is designed to facilitate the acquisition of foreign intelligence information concerning non-U.S. persons located outside the United States. It cannot be used to intentionally target any U.S. citizen, any other U.S. person, or anyone located within the United States.
Activities authorized by Section 702 are subject to oversight by the Foreign Intelligence Surveillance Court, the Executive Branch, and Congress. They involve extensive procedures, specifically approved by the court, to ensure that only non-U.S. persons outside the U.S. are targeted, and that minimize the acquisition, retention and dissemination of incidentally acquired information about U.S. persons.
Article Link: Intelligence Program Gives US Government Direct Access to Customer Data on Apple Servers [Update: Apple Denies]

