I was just reading HackerNews and came across a startling discovery.
If a person somehow managed to get access to your computer they can use the security command in the Terminal to get access to ALL your login usernames and passwords.
You can read more about this here: https://news.ycombinator.com/item?id=4518873
The actual command, if you'd like to see how easy it actually is for the system to just spew your passwords in the Terminal, is the one given below. Just copy and paste into the terminal and hit enter. Notice how you don't even have to type sudo in front (which means it doesn't require your password at all before it runs):
You can press Control-C in the Terminal to manually quit the dumping process.
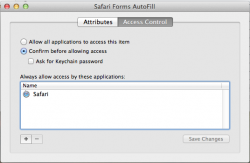
The only dialog that shows up is the allow or deny option and if you click allow, the password gets dumped into the Terminal.
The only way to prevent this is to actually click on the Lock icon in the Keychain app or set up the autolocking feature of the app by following these steps:
Open "Keychain Access". Right click on "login" and select the "change settings for Keychain login" item. Check the box next to "lock after x minutes of inactivity". I set it up for 15 minutes. The only downside to that is, you have to enter your password every time the system asks to access the login keychain which is tedious if you have a big password like I do.
I don't really understand if this is a security flaw or not for now. From what people have said, it may be a conscious decision of Apple to unlock the login keychain so that the user does not have to type their password in every time the system asks. What do you guys think?
If a person somehow managed to get access to your computer they can use the security command in the Terminal to get access to ALL your login usernames and passwords.
You can read more about this here: https://news.ycombinator.com/item?id=4518873
The actual command, if you'd like to see how easy it actually is for the system to just spew your passwords in the Terminal, is the one given below. Just copy and paste into the terminal and hit enter. Notice how you don't even have to type sudo in front (which means it doesn't require your password at all before it runs):
Code:
security dump-keychain -d ~/Library/Keychains/login.keychainYou can press Control-C in the Terminal to manually quit the dumping process.
The only dialog that shows up is the allow or deny option and if you click allow, the password gets dumped into the Terminal.
The only way to prevent this is to actually click on the Lock icon in the Keychain app or set up the autolocking feature of the app by following these steps:
Open "Keychain Access". Right click on "login" and select the "change settings for Keychain login" item. Check the box next to "lock after x minutes of inactivity". I set it up for 15 minutes. The only downside to that is, you have to enter your password every time the system asks to access the login keychain which is tedious if you have a big password like I do.
I don't really understand if this is a security flaw or not for now. From what people have said, it may be a conscious decision of Apple to unlock the login keychain so that the user does not have to type their password in every time the system asks. What do you guys think?


 iMac
iMac