
Apple's bug bounty program has been available to select security researchers for almost a year now, but according to a new report from Motherboard, most researchers prefer not to share bugs with Apple due to low payouts. More money can be obtained from third-party sources for bugs in Apple software.
Motherboard spoke to several members of Apple's bug bounty program with the condition of anonymity. Every single one said they had yet to report a bug to Apple and did not know anyone who had. iOS bugs are "too valuable to report to Apple," according to Patrick Wardle, a Synack researcher and former NSA hacker who was invited to the bug bounty program last year."People can get more cash if they sell their bugs to others," said Nikias Bassen, a security researcher for the company Zimperium, and who joined Apple's program last year. "If you're just doing it for the money, you're not going to give [bugs] to Apple directly."
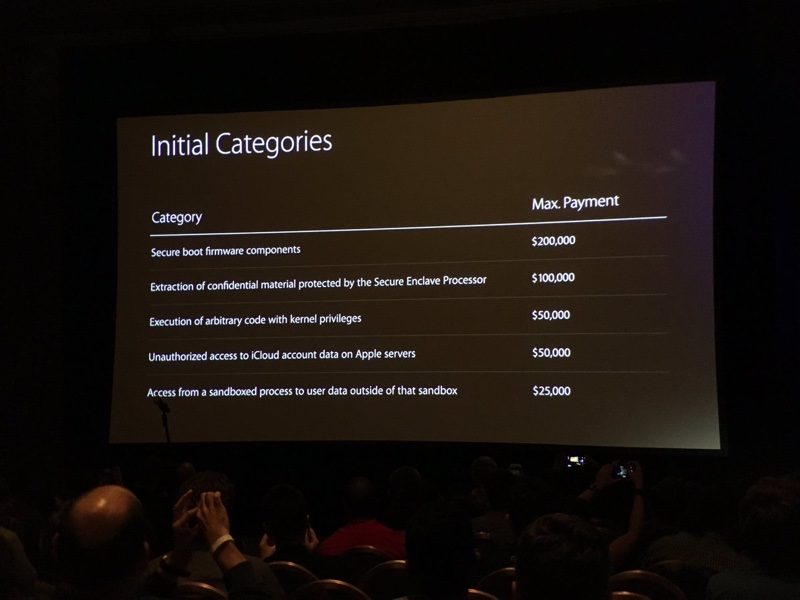
Apple first introduced its bug bounty program in August of 2016 at the Black Hat Conference, an annual global InfoSec event. Apple offers bounties of up to $200,000 depending on the vulnerability. Secure boot firmware components earn $200,000 at the high end, while smaller vulnerabilities, like access from a sandboxed process to user data outside of the sandbox, will earn $25,000.
Article Link: Security Researchers Don't Think Apple Pays Enough for Bug Bounties

