It is kind of funny that people get so worked up about credit card numbers. Honestly, a criminal could already have your credit card number by random chance.
For example, http://mediakey.dk/~cc/wp-dyn/credit-card-number-generator.php
Really, it is just a number in a specific format. There is nothing magical about a credit card number.
With the Sony PSN breach and recent Mac malware in the wild, there is a lot of talk on the internet and in threads in this forum about online credit card fraud. Honestly, credit card fraud is just as likely to occur independent of the internet. In reality, your social security number and bank account number are much more critical than your credit card number because those numbers are used to get big loans for amounts much greater than a credit card limit. The big fish of online financial fraud is logging into another persons online banking to maximize the profitability of the crime by facilitating identity theft above and beyond credit card purchases.
Online identity theft requires more than a credit card number. Often more specific information is required about the individual. That more specific information about an individual could already be online depending on how much information a user includes in online public profiles, such as MySpace and Facebook. Even all this information will not allow someone access to online banking accounts.
More sophisticated malware uses a keylogger to collect passwords to gain information that will expose online banking credentials; specifically, an online banking login password. Keyloggers facilitate this type of fraud by collecting passwords to online banking, email, and social networking sites. Email accounts are used to reset other passwords. Social networking sites provide other needed information if not already easily accessible.
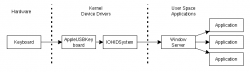
Mac OS X implements two user space security mechanisms that prevent keyloggers and other malware from logging these passwords unless social engineering tactics are successful or the exploitation includes privilege escalation. Privilege escalation is rare in OS X so prevention is basically up to the user. The first security mechanism is called EnableSecureEventInput which prevents keyboard events related to security sensitive logins being logged when exiting IOHIDSystem on the way to Window Server. The other security mechanism is called NSSecureTextField which prevents password from being viewed or captured in the user interface by form grabbers.
Keyloggers installed in kernel space are able to log these protected passwords. Looking at the source code for logkext shows it interacts with IOHIKeyboard located in the IOHIDSystem bundle to log keyboard events in kernel space. To locate these items in finder, do an advanced search in Finder for IOHIDFamily and search inside the package contents for IOHIDSystem. Kernel space keyloggers require user authentication to install unless the exploit includes privilege escalation. These kernel device drivers are protected by the discretionary access controls of OS X unless using the root user account.
For example, http://mediakey.dk/~cc/wp-dyn/credit-card-number-generator.php
Really, it is just a number in a specific format. There is nothing magical about a credit card number.
With the Sony PSN breach and recent Mac malware in the wild, there is a lot of talk on the internet and in threads in this forum about online credit card fraud. Honestly, credit card fraud is just as likely to occur independent of the internet. In reality, your social security number and bank account number are much more critical than your credit card number because those numbers are used to get big loans for amounts much greater than a credit card limit. The big fish of online financial fraud is logging into another persons online banking to maximize the profitability of the crime by facilitating identity theft above and beyond credit card purchases.
Online identity theft requires more than a credit card number. Often more specific information is required about the individual. That more specific information about an individual could already be online depending on how much information a user includes in online public profiles, such as MySpace and Facebook. Even all this information will not allow someone access to online banking accounts.
More sophisticated malware uses a keylogger to collect passwords to gain information that will expose online banking credentials; specifically, an online banking login password. Keyloggers facilitate this type of fraud by collecting passwords to online banking, email, and social networking sites. Email accounts are used to reset other passwords. Social networking sites provide other needed information if not already easily accessible.
Mac OS X implements two user space security mechanisms that prevent keyloggers and other malware from logging these passwords unless social engineering tactics are successful or the exploitation includes privilege escalation. Privilege escalation is rare in OS X so prevention is basically up to the user. The first security mechanism is called EnableSecureEventInput which prevents keyboard events related to security sensitive logins being logged when exiting IOHIDSystem on the way to Window Server. The other security mechanism is called NSSecureTextField which prevents password from being viewed or captured in the user interface by form grabbers.
Keyloggers installed in kernel space are able to log these protected passwords. Looking at the source code for logkext shows it interacts with IOHIKeyboard located in the IOHIDSystem bundle to log keyboard events in kernel space. To locate these items in finder, do an advanced search in Finder for IOHIDFamily and search inside the package contents for IOHIDSystem. Kernel space keyloggers require user authentication to install unless the exploit includes privilege escalation. These kernel device drivers are protected by the discretionary access controls of OS X unless using the root user account.