Got a tip for us?
Let us know
Become a MacRumors Supporter for $50/year with no ads, ability to filter front page stories, and private forums.
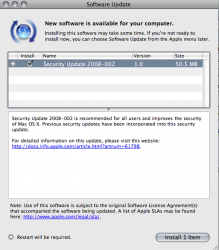
Apple release Security Update 2008-002
- Thread starter James17
- Start date
- Sort by reaction score
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Axemantitan
macrumors 6502a
Security Update 2008-002
AFP Client - Accessing a maliciously crafted afp:// URL may lead to an application termination or arbitrary code execution
AFP Client - Accessing a maliciously crafted afp:// URL may lead to an application termination or arbitrary code execution
Multiple stack buffer overflow issues exist in AFP Client's handling of afp:// URLs. By enticing a user to connect to a malicious AFP Server, an attacker may cause an unexpected application termination or arbitrary code execution. This update addresses the issues through improved bounds checking.
AFP Server - Cross-realm authentication with AFP Server may be bypassed
An implementation issue exists in AFP Server's check of Kerberos principal realm names. This may allow unauthorized connections to the server, when cross-realm authentication with AFP Server is used. This update addresses the issue by through improved checks of Kerberos principal realm names. This issue does not affect systems running Mac OS X v10.5 or later. Credit to Ragnar Sundblad of KTH - Royal Institute of Technology, Stockholm, Sweden for reporting this issue.
Apache - Multiple vulnerabilities in Apache 1.3.33 and 1.3.39Apache is updated to version 1.3.41 to address several vulnerabilities, the most serious of which may lead to arbitrary code execution. Further information is available via the Apache web site at http://httpd.apache.org For Mac OS X v10.5, Apache version 1.3.x is only shipped on Server configurations. mod_ssl is also updated from version 2.8.24 to 2.8.31 to match the upgraded Apache; no security fixes are included in the update.
Apache - Multiple vulnerabilities in Apache 2.2.6Apache is updated to version 2.2.8 to address several vulnerabilities, the most serious of which may lead to cross-site scripting. Further information is available via the Apache web site at http://httpd.apache.org
AppKit - Usage of the NSDocument API to may lead to arbitrary code executionA stack buffer overflow exists in the NSDocument API's handling of file names. On most file systems, this issue is not exploitable. This update addresses the issue through improved bounds checking. This issue does not affect systems running Mac OS X v10.5 or later.
AppKit - A local user may be able to execute arbitrary code with system privilegesA mach port in NSApplication intended for inter-thread synchronization is unintentionally available for inter-process communication. By sending maliciously crafted messages to privileged applications in the same bootstrap namespace, a local user may cause arbitrary code execution with the privileges of the target application. This update addresses the issue by removing the mach port in question and using another method to synchronize. This issue does not affect systems running Mac OS X v10.5 or later.
AppKit - Visiting a maliciously crafted website may lead to arbitrary code executionMultiple integer overflow vulnerabilities exist in the parser for a legacy serialization format. By causing a maliciously formatted serialized property list to be parsed, an attacker could trigger a heap-based buffer overflow which may lead to arbitrary code execution. This update addresses the issue by performing additional validation of serialized input. This issue does not affect systems running Mac OS X v10.5 or later.
AppKit - Querying a network printer may cause an unexpected application termination or arbitrary code executionA stack based buffer overflow exists in AppKit's handling of PPD files. By enticing a user to query a network printer, an attacker may cause an unexpected application termination or arbitrary code execution. This update addresses the issue through improved handling of PPD files. This issue does not affect systems running Mac OS X v10.5 or later.
Application Firewall - The German translation of the Application Firewall preference pane was misleadingThe "Set access for specific services and applications" radio button of the Application Firewall preference pane was translated into German as "Zugriff auf bestimmte Dienste und Programme festlegen", which is "Set access to specific services and applications". This might lead a user to believe that the listed services were the only ones that would be permitted to accept incoming connections. This update addresses the issue by changing the German text to semantically match the English text. This issue does not affect systems prior to Mac OS X v10.5.
CFNetwork - A malicious proxy server may spoof secure websitesA malicious HTTPS proxy server may return arbitrary data to CFNetwork in a 502 Bad Gateway error. A malicious proxy server could use this to spoof secure websites. This update addresses the issue by returning an error on any proxy error, instead of returning the proxy-supplied data. This issue is already addressed in systems running Mac OS X v10.5.2.
ClamAV - Multiple vulnerabilities in ClamAV 0.90.3Multiple vulnerabilities exist in ClamAV 0.90.3 provided with Mac OS X Server v10.5 systems, the most serious of which may lead to arbitrary code execution. This update addresses the issue by updating to ClamAV 0.92.1. Further information is available via the ClamAV website at www.clamav.net
ClamAV - Multiple vulnerabilities in ClamAV 0.88.5Multiple vulnerabilities exist in ClamAV 0.88.5 provided with Mac OS X Server v10.4.11, the most serious of which may lead to arbitrary code execution. This update addresses the issue by updating to ClamAV 0.92.1. Further information is available via the ClamAV website at www.clamav.net
CoreFoundation - A local user may be able to execute arbitrary code with system privilegesAn integer overflow exists in CoreFoundation's handling of time zone data. This may allow a local user to cause arbitrary code execution with system privileges. This update addresses the issue through improved bounds checking on time zone data files. This issue does not affect systems running Mac OS X v10.5 or later.
CoreServices - Visiting a website could cause files to be opened in AppleWorksFiles with names ending in ".ief" can be automatically opened in AppleWorks if Safari's "Open 'Safe' files" preference is enabled. This is not the intended behavior and could lead to security policy violations. This update addresses the issue by removing ".ief" from the list of safe file types. This issue only affects systems prior to Mac OS X v10.5 with AppleWorks installed.
CUPS - A remote attacker may be able to cause an unexpected application termination if printer sharing is enabledA memory leak exists in CUPS. By sending a large number of requests to add and remove shared printers, an attacker may be able to cause a denial of service. This issue can not result in arbitrary code execution. This update addresses the issue through improved memory management. This issue does not affect systems prior to Mac OS X v10.5.
CUPS - A remote attacker may be able to cause an unexpected application termination or arbitrary code execution if printer sharing is enabledA heap buffer overflow exists in the CUPS interface's processing of search expressions. If printer sharing is enabled, a remote attacker may be able to cause an unexpected application termination or arbitrary code execution with system privileges. If printer sharing is not enabled, a local user may be able to gain system privileges. This update addresses the issue by performing additional bounds checking. This issue does not affect systems prior to Mac OS X v10.5. Credit to regenrecht working with the VeriSign iDefense VCP for reporting this issue.
CUPS - Multiple vulnerabilities in CUPS may lead to an unexpected application termination or arbitrary code execution with system privilegesMultiple input validation issues exist in CUPS, the most serious of which may lead to arbitrary code execution with system privileges. This update addresses the issues by updating to CUPS 1.3.6. These issues do not affect systems prior to Mac OS X v10.5.
curl - Running curl with a maliciously crafted URL may lead to an unexpected application termination or arbitrary code executionA one byte buffer overflow exists in curl 7.13.1. By enticing a user to run curl with a maliciously crafted URL, an attacker may cause an unexpected application termination or arbitrary code execution. This update addresses the issue by updating curl to version 7.16.3. Crash Reporter was updated to match the curl changes. This issue does not affect systems running Mac OS X v10.5 or later.
Emacs - Format string vulnerability in Emacs Lisp may lead to an unexpected application termination or possibly arbitrary code executionA stack buffer overflow exists in Emacs' format function. By exploiting vulnerable Emacs Lisp which allows an attacker to provide a format string containing a large precision value, an attacker may cause an unexpected application termination or possibly arbitrary code execution. Further information on the patch applied is available via the Savannah Emacs website at http://cvs.savannah.gnu.org/viewvc/emacs/emacs/src/editfns.c?r1=1.439.2.3&r2=1.439.2.9&view=patch
Emacs - Safe mode checks in Emacs may be bypassedA logic error in Emacs' hack-local-variable function allows any local variable to be set, even if `enable-local-variables' is set to :safe. By enticing a user to load a file containing a maliciously crafted local variables declaration, a local user may cause an unauthorized modification of Emacs Lisp variables leading to arbitrary code execution. This issue has been fixed through improved :safe mode checks. The patch applied is available via the Savannah Emacs website at http://cvs.savannah.gnu.org/viewvc/...37&r2=1.938&sortby=date&root=emacs&view=patch This issue does not affect systems prior to Mac OS X v10.5.
file - Running the file command on a maliciously crafted file may lead to an unexpected application termination or arbitrary code executionAn integer overflow vulnerability exists in the file command line tool, which may lead to an unexpected application termination or arbitrary code execution. This update addresses the issue through improved bounds checking. This issue does not affect systems running Mac OS X v10.5 or later. Credit to Colin Percival of the FreeBSD security team for reporting this issue.
Foundation - Usage of the NSSelectorFromString API may result in an unexpected method being calledAn input validation issue exists in the NSSelectorFromString API. Passing it a malformed selector name may result in the return of an unexpected selector, which could lead to an unexpected application termination or arbitrary code execution. This update addresses the issue by performing additional validation on the selector name. This issue does not affect systems running Mac OS X v10.5 or later.
Foundation - A local user can interfere in other users' file operations and may be able to obtain elevated privilegesWhen performing a recursive file copying operation, NSFileManager creates directories as world-writable, and only later restricts the permissions. This creates a race condition during which a local user can manipulate the directory and interfere in subsequent operations. This may lead to a privilege escalation to that of the application using t he API. This update addresses the issue by creating directories with restrictive permissions. This issue does not affect systems running Mac OS X v10.5 or later.
Foundation - Programs using the NSFileManager API could be manipulated to execute arbitrary codeA long pathname with an unexpected structure can expose a stack buffer overflow vulnerability in NSFileManager. Presenting a specially crafted path to a program using NSFileManager could lead to the execution of arbitrary code. This update addresses the issue by ensuring a properly sized destination buffer. This issue does not affect systems running Mac OS X v10.5 or later.
Foundation - Visiting a maliciously crafted website may lead to a denial of service or arbitrary code executionA thread race condition exists in NSURLConnection's cache management, which can cause a deallocated object to receive messages. Triggering this issue may lead to a denial of service, or arbitrary code execution with the privileges of Safari or another program using NSURLConnection. This update addresses the issue by removing an unsynchronized caching operation. This issue does not affect systems running Mac OS X v10.5 or later. Credit to Daniel Jalkut of Red Sweater Software for reporting this issue.
Foundation - Processing an XML document may lead to an unexpected application termination or arbitrary code executionA race condition exists in NSXML. By enticing a user to process an XML file in an application which uses NSXML, an attacker may cause an unexpected application termination or arbitrary code execution. This update addresses the issue through improvements to the error handling logic of NSXML. This issue does not affect systems running Mac OS X v10.5 or later.
Help Viewer - Accessing a maliciously crafted help: URL may lead to arbitrary Applescript executionA malicious help:topic_list URL may insert arbitrary HTML or JavaScript into the generated topic list page, which may redirect to a Help Viewer help:runscript link that runs Applescript. This update addresses the issue by performing HTML escaping on the URL data used in help topic lists before building the generated page. Credit to Brian Mastenbrook for reporting this issue.
Image Raw - Viewing a maliciously crafted image may lead to an unexpected application termination or arbitrary code executionA stack based buffer overflow exists in the handling of Adobe Digital Negative (DNG) image files. By enticing a user to open a maliciously crafted image file, an attacker may cause an unexpected application termination or arbitrary code execution. This update addresses the issue through improved validation of DNG image files. This issue does not affect systems prior to Mac OS X v10.5. Credit to Clint Ruoho of Laconic Security for reporting this issue.
Kerberos - Multiple vulnerabilities in MIT Kerberos 5 may lead to an unexpected application termination or arbitrary code execution with system privilegesMultiple memory corruption issues exist in MIT Kerberos 5, which may lead to an unexpected application termination or arbitrary code execution with system privileges. Further information on the issues and the patches applied is available via the MIT Kerberos website at http://web.mit.edu/Kerberos/ CVE-2008-0062 and CVE-2008-0063 do not affect systems running Mac OS X v10.5 or later. CVE-2007-5901 does not affect systems prior to Mac OS X v10.4.
libc - Applications that use the strnstr API could be vulnerable to a denial of serviceAn off by one issue exists in Libsystem's strnstr(3) implementation. Applications that use the strnstr API can read one byte beyond the limit specified by the user, which may lead to an unexpected application termination. This update addresses the issue through improved bounds checking. This issue does not affect systems running Mac OS X v10.5 or later. Credit to Mike Ash of Rogue Amoeba Software for reporting this issue.
mDNSResponder - A local user may be able to execute arbitrary code with system privilegesA format string issue exists in mDNSResponderHelper. By setting the local hostname to a maliciously crafted string, a local user could cause a denial of service or arbitrary code execution with the privileges of mDNSResponderHelper. This update addresses the issue by using a static format string. This issue does not affect systems prior to Mac OS X v10.5.
notifyd - A local user may be able to deny access to notificationsnotifyd accepts Mach port death notifications without verifying that they come from the kernel. If a local user sends fake Mach port death notifications to notifyd, applications that use the notify(3) API to register for notifications may never receive the notifications. This update addresses the issue by only accepting Mach port death notifications from the kernel. This issue does not affect systems running Mac OS X v10.5 or later.
OpenSSH - A remote attacker may be able to execute arbitrary code with elevated privilegesOpenSSH forwards a trusted X11 cookie when it cannot create an untrusted one. This may allow a remote attacker to gain elevated privileges. This update addresses the issue by updating OpenSSH to version 4.7. Further information is available via the OpenSSH website at http://www.openssh.org/txt/release-4.7
pax archive utility - Running the pax command on a maliciously crafted archive may lead to arbitrary code executionThe pax command line tool does not check a length in its input before using it as an array index, which may lead to an unexpected application termination or arbitrary code execution. This update addresses the issue by checking the index. This issue does not affect systems prior to Mac OS X v10.5.
PHP - Multiple vulnerabilities in PHP 5.2.4PHP is updated to version 5.2.5 to address multiple vulnerabilities, the most serious of which may lead to arbitrary code execution. Further information is available via the PHP website at http://www.php.net/ PHP version 5.2.x is only provided with Mac OS X v10.5 systems.
PHP - Multiple vulnerabilities in PHP 4.4.7PHP is updated to version 4.4.8 to address multiple vulnerabilities, the most serious of which may lead to arbitrary code execution. Further information is available via the PHP website at http://www.php.net/
Podcast Producer - Podcast Capture exposes passwords to other local usersThe Podcast Capture application provides passwords to a subtask through the arguments, potentially exposing the passwords to other local users. This update corrects the issue by providing passwords to the subtask through a pipe. This issue does not affect systems prior to Mac OS X v10.5. Credit to Maximilian Reiss of Chair for Applied Software Engineering, TUM for reporting this issue.
Preview - Saving to encrypted PDF in Preview produces files that may be read without the passwordWhen Preview saves a PDF file with encryption, it uses 40-bit RC4. This encryption algorithm may be broken with significant but readily available computing power. A person with access to the file may apply a brute-force technique to view it. This update enhances the encryption to 128-bit RC4.
Printing - Printing to encrypted PDF produces files that may be read without the `open' passwordPrinting to a PDF file and setting an 'open' password uses 40-bit RC4. This encryption algorithm may be broken with significant but readily available computing power. A person with access to the file may apply a brute-force technique to view it. This update enhances the encryption to 128-bit RC4. This issue does not affect systems prior to Mac OS X v10.5.
Printing - Printing to an authenticated print queue may disclose login credentialsAn information disclosure issue exists in the handling of authenticated print queues. When starting a job on an authenticated print queue, the credentials used for authentication may be saved to disk. This update addresses the issue by removing user credentials from printing presets before saving them to disk. This issue does not affect systems prior to Mac OS X v10.5.
System Configuration - A local user may be able to execute arbitrary code with system privilegesThe privileged tool NetCfgTool uses distributed objects to communicate with untrusted client programs on the local machine. By sending a maliciously crafted message, a local user can bypass the authorization step and may cause arbitrary code execution with the privileges of the privileged program. This update addresses the issue by performing additional validation of distributed objects.
UDF - Opening a maliciously crafted disk image may lead to an unexpected system shutdownA null pointer dereference issue exists in the handling of Universal Disc Format (UDF) file systems. By enticing a user to open a maliciously crafted disk image, an attacker may cause an unexpected system shutdown. This update addresses the issue through improved validation of UDF file systems. This issue does not affect systems prior to Mac OS X v10.5. Credit to Paul Wagland of Redwood Software, and Wayne Linder of Iomega for reporting this issue.
Wiki Server - A user with access to edit wiki content may be able to execute arbitrary commands as the wiki serverA path traversal issue exists in the Mac OS X v10.5 Server Wiki Server. Attackers with access to edit wiki content may upload files that leverage this issue to place content wherever the wiki server can write, which may lead to arbitrary code execution with the privileges of the wiki server. This update addresses the issue through improved file name handling. This issue does not affect systems prior to Mac OS X v10.5. Credit to Rodrigo Carvalho, from the Core Security Consulting Services (CSC) team of CORE Security Technologies.
X11 - Multiple Vulnerabilities in X11 X Font Server (XFS) 1.0.4Multiple vulnerabilities exist in X11 X Font Server (XFS) 1.0.4, the most serious of which may lead to arbitrary code execution. This update addresses the issue by updating to version 1.0.5. Further information is available via the X.Org website at http://www.x.org/wiki/Development/Security These issues are already addressed in systems running Mac OS X v10.5.2.
X11 - Multiple vulnerabilities in X11's libpng 1.2.8The PNG reference library (libpng) is updated to version 1.2.24 to address several vulnerabilities, the most serious of which may lead to a remote denial of service or arbitrary code execution. Further information is available via the libpng website at http://www.libpng.org/pub/png/libpng.html This issue affects libpng within X11. It does not affect systems prior to Mac OS X v10.5.
X11 - Multiple vulnerabilities in the X11 serverNumerous vulnerabilities in the X11 server allow execution of arbitrary code with the privileges of the user running the X11 server if the attacker can authenticate to the X11 server. This is a security vulnerability only if the X11 server is configured to not require authentication, which Apple does not recommend. This update fixes the issue by applying the updated X.Org patches. Further information is available via the X.Org website at http://www.x.org/wiki/Development/Security
philgilder
macrumors 68000
whenever they are neededAs a brand new Mac owner, I'm curious, how often are these updates issued? Is this akin to "Patch Tuesday" for Windows users?
theres no regular update schedule
just be glad apple doesnt take a year and a half to get out one service pack, compared to leopard thats had 2 'service packs' in 3 months or so...
see the post above yoursUh, was this really necessary?
sblasl
macrumors 6502a
Here is the stand alone installer for intel machines 103MB.
http://www.apple.com/support/downloads/securityupdate2008002v10universal.html
And the PPC stand alone installer 68MB.
http://www.apple.com/support/downloads/securityupdate2008002v10ppc.html
When did Apple start to providing such in-depth support documents for security updates?
http://www.apple.com/support/downloads/securityupdate2008002v10universal.html
And the PPC stand alone installer 68MB.
http://www.apple.com/support/downloads/securityupdate2008002v10ppc.html
When did Apple start to providing such in-depth support documents for security updates?
Cameront9
macrumors 65816
As a brand new Mac owner, I'm curious, how often are these updates issued? Is this akin to "Patch Tuesday" for Windows users?
About every 1-2 months, I think. Not quite as frequent as patch tuesday.
xUKHCx
Administrator emeritus
When did Apple start to providing such in-depth support documents for security updates?
A long time
25 Jan 2005 to Present
03-Oct-03 to 11 - Jan -2005
2003 and earlier
edit:
50.5 MB here on 10.5.2.
I had no idea it was so all-encompassing by the brief description on the MR home page. So thanks, Doctor, for the detail in what this update entailed.
Morod
You can see all the security issues regarding the updates from the link provided in Software Update. Although Doctor Q listed (all 46) of them here for you, so just for future reference.
dwman
macrumors 6502
Sorry, I should have clarified. I wasn't implying that the update wasn't necessary, but the need for the poster to list every single bug fix from Apple's support page. I think a link would have more then sufficed.
/dev/toaster
macrumors 68020
xUKHCx
Administrator emeritus
Thanks for mirroring the patch notes, it appears the Apple doc site is down 🙁
It's not for me, direct link to the patch notes.
japanime
macrumors 68030
Sorry, I should have clarified. I wasn't implying that the update wasn't necessary, but the need for the poster to list every single bug fix from Apple's support page. I think a link would have more then sufficed.
As a (relatively) longtime user of these forums, I find it quite handy when other members list the bug fixes rather than just provide a link.
To paraphrase the old Trix commercials, "Silly newbie! Links are for kids." 😀
skiesforme
macrumors 6502
I have come across this complaint hundreds of times and faced it myself 3 times (new router/new MB/MBP). Solved it each time !Who cares about uptime,keep the fixes coming.All we need is the wi-fi fix and then I will forgive Apple for a few days 😱
What exactly is your problem ? Is it network drop-outs ? Poor bandwidth ? Poor reception ?
I have a SR 2.2 MB and a Penryn 2.4 MBP. Used to have a crappy Trendnet 432BRP 802.11 b/g and now got a 802.11n APExpress. Faced wireless issues each time while setting up the network (1st time) but fixed it every single time !
What did I change ? Channel (1/6/11) or DNS (4.2.2.1/2 , OpenDNS.com)
Do it once and once it starts working for you it never goes bad. My 1st Penryn MBP had a faulty Airport and DNS/Channel changes did not work. But I got it replaced and now it's all good !
Tools: speakeasy/internetfrog; iStumbler ; Router config/Airport Utility.
Glideslope
macrumors G3
Uh, was this really necessary? 😕
Yes. The Goose Bumps are just receding.
powerbuddy
macrumors 6502
joseph2166
macrumors 6502
A second update requiring a reboot in one day?
Seriously, they couldn't just hold Safari until this was ready so we'd only have to reboot once?
The things we go through