Researcher Bhavuk Jain in April discovered a critical Sign in With Apple vulnerability that could have resulted in a takeover of some user accounts. The bug was specific to third party apps that used Sign in With Apple and didn't implement additional security measures.
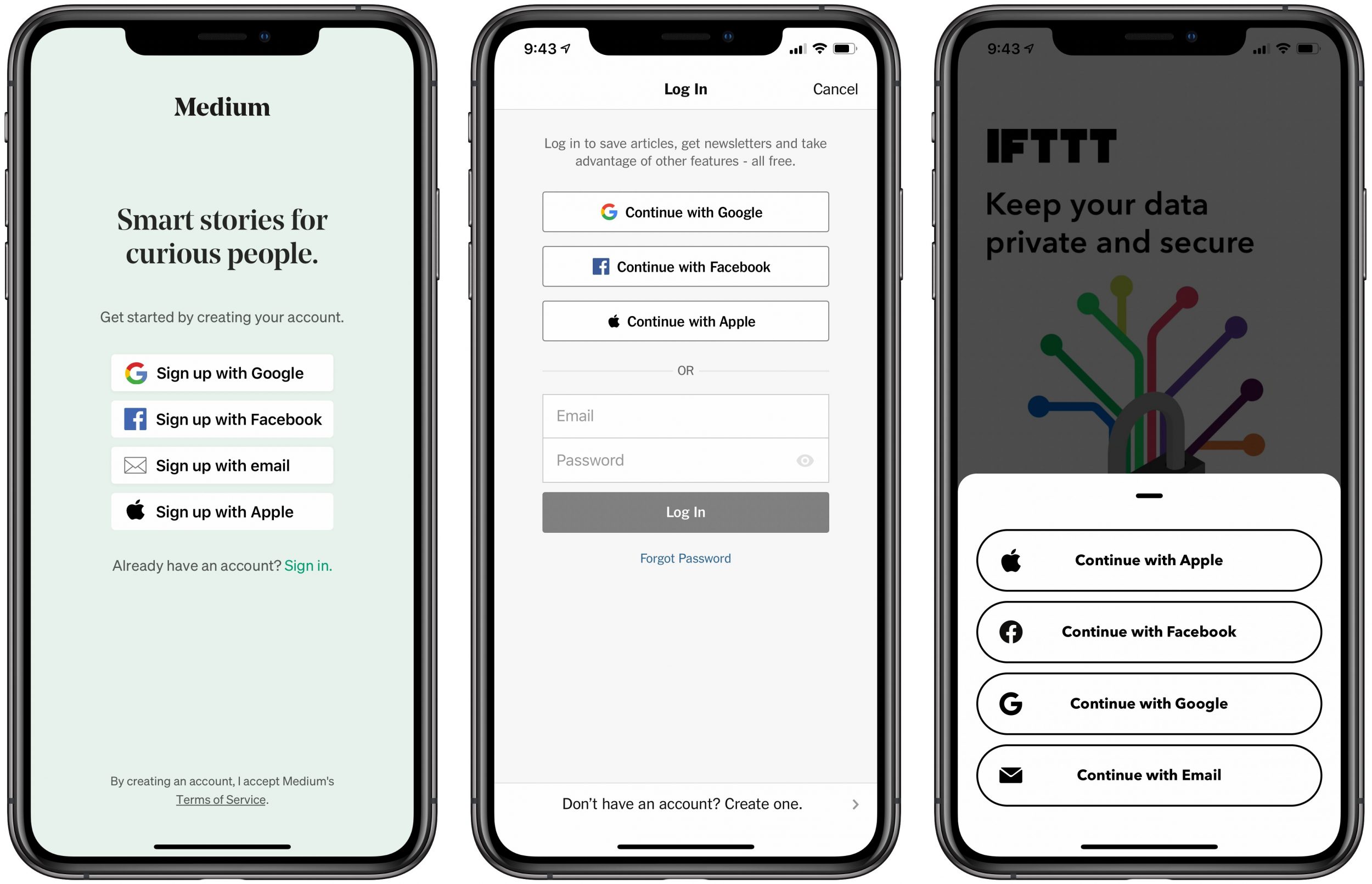
Jain notes that Sign in With Apple works by authenticating a user through a JWT (JSON Web Token) or a code that's generated by Apple's server. Apple then gives users the option to share either the email tied to their Apple ID or a private relay email address,which creates a JWT that's used to log in a user.
Jain then discovered that once JWTs for both Apple ID emails and private relay email addresses were requested and the token's signature was verified using Apple's public key, it "showed as valid." Should the bug have not been discovered, a JWT could be created and used to gain access to one's account.
In an interview with The Hacker News, Jain spoke about the severity of the bug:
The impact of the this vulnerability was quite critical as it could have allowed a full account takeover. Many developers have integrated Sign in with Apple since it is mandatory for applications that support other social logins. To name a few that use Sign in with Apple - Dropbox, Spotify, Airbnb, Giphy (now acquired by Facebook).
According to Jain, Apple conducted an investigation and concluded that no accounts were compromised using this method before the vulnerability was patched. Jain was paid $100,000 by Apple under its Apple Security Bounty Program for reporting the bug.
Article Link: Now Patched 'Sign in With Apple' Bug Left Users Open to Attack
Last edited: