I only have partial information, and do not 100% know the exact OSx version or how full the drive was, but I think it was pretty topped out. No recent backups, important data, and I have already put the fear of god into them regarding backups so this doesn't happen again. They have a several months old timemachine backup available so if there may be something useful there like a partition table or encryption key I need I may be able to get access to it.
The set up, steps taken and how we got this far:
-Friend's 2015 Macbook Air stopped turning on. May have had a bad shutdown involved. Dead logic board.
-Drive Enclosure is obtained. The drive would not successfully boot into any macs at the Apple store. Genius Bar may or may not have run some commands to try and recover things. Report that part of the SSD that managed FileVault is probably damaged.
-Friend's university tech shop takes a look with no luck.
-They stress how important some of their research data is, I refer them to Drive Savers out of an abundance of caution.
-Drive Savers tries to hook it into a system (??), says it isn't working, sends them on their way within 15 minutes or so.
-Bottom line, the usual boot off of it on a different mac, etc troubleshooting isn't working.
-I take pity on them and have taken this on as a side project, believe this is an encrypted APFS drive.
-I manage to capture a seemingly 100% good 500GB disk image, and mirror to a 2TB external drive, directly off the bad drive in the enclosure on an Ubuntu system using ddrescue. For anyone else going through this with a drive that keeps dropping connection, try a powered USB hub.
ddrescue commands used
No bad sectors or errors on both, a quick look at the image in a hex editor and yep, stuff is in there alright. Have a backup of the dmg just in case.
Feeling a new level of confidence that I won't fry the last hope we have of getting this data back by hammering it with attempts, it's time to jump on my wife's Macbook Pro and see what we can see. Unfortunately, not being a mac guy, I am hitting some walls, probably caused by my own ignorance of the underlying system and available commands. I am comfortable at a command line, but I am not a mac user.
Mac Attempts and command results:
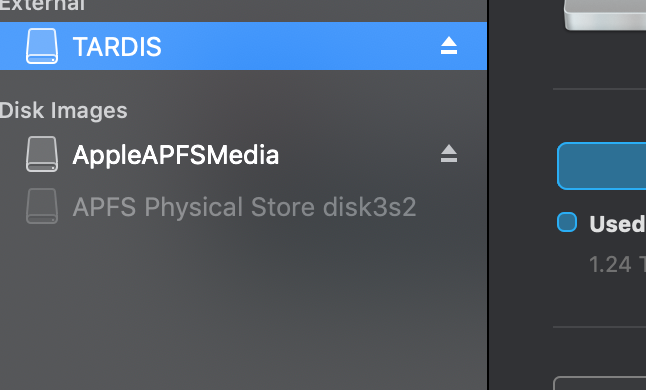
DISK UTILITY File>Open Disk Image>RescueImage1.dmg
Hangs and very briefly it appears on the left showing the following then it immediately disappears
Hooking the cloned drive up
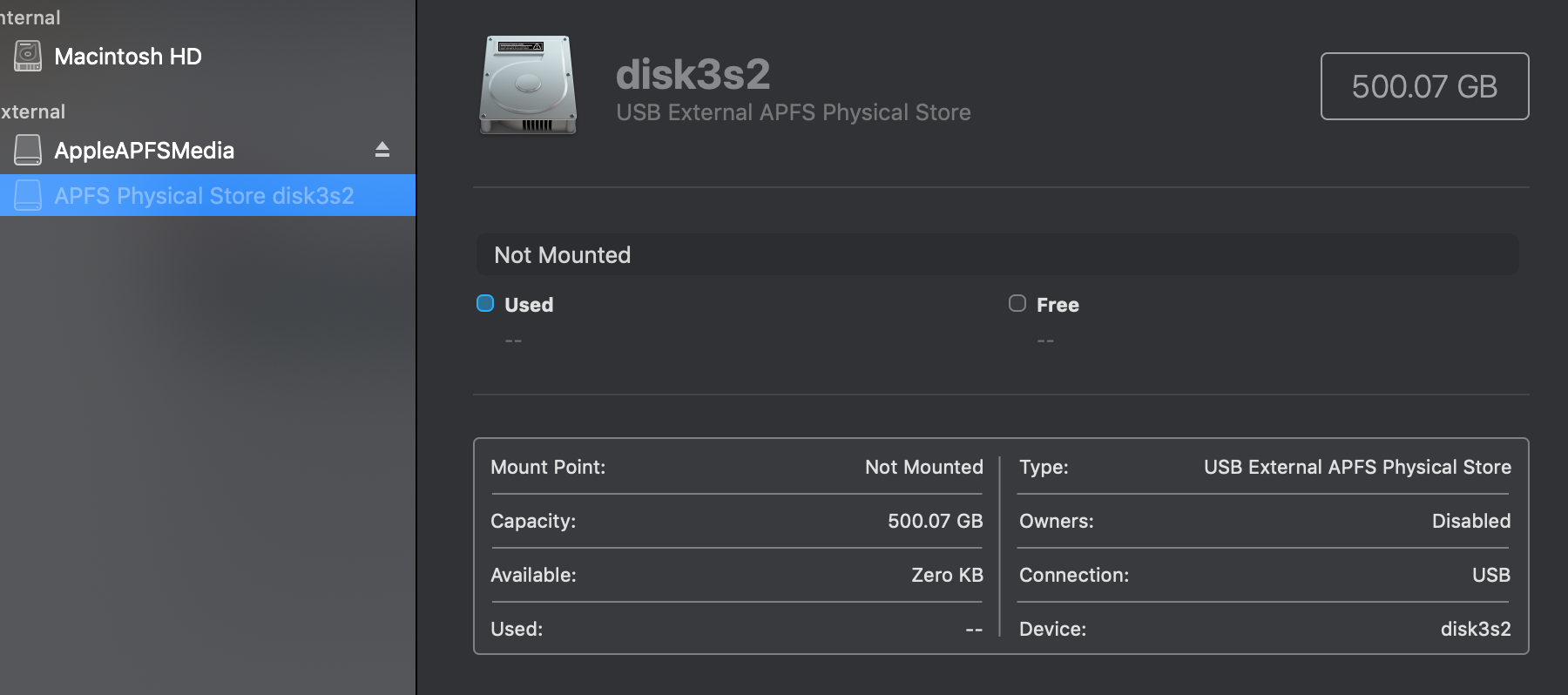
Click Mount on disk3s2 and nothing happens, no feedback
File->Get Info on disk3s2
Volume type : APFS Physical Store
BSD device node : disk3s2
Connection : USB
Device tree path : IODeviceTree:/PCI0@0/XHC1@14
Writable : No
Is case-sensitive : No
Volume capacity : 500,068,036,608
Owners enabled : No
Is encrypted : No
Can be verified : Yes
Can be repaired : Yes
Bootable : No
Journaled : No
Disk number : 3
Partition number : 2
Media name :
Media type : Generic
Ejectable : Yes
Solid state : No
S.M.A.R.T. status : Not Supported
Parent disks : disk3
File->Get Info on AppleAPFSMedia
Volume type : Uninitialized
BSD device node : disk4
Connection : USB
Device tree path : IODeviceTree:/PCI0@0/XHC1@14
Writable : No
Is case-sensitive : No
Volume capacity : 500,068,036,608
Available space (Purgeable + Free) : 0
Purgeable space : 0
Free space : 0
Used space : 500,068,036,608
Owners enabled : No
Is encrypted : No
Can be verified : No
Can be repaired : No
Bootable : No
Journaled : No
Disk number : 4
Media name : AppleAPFSMedia
Media type : Generic
Ejectable : Yes
Solid state : No
S.M.A.R.T. status : Not Supported
Disk Utility First Aid Results
Still no mount on disk3s2. I think I have exhausted my Disk Utility GUI options so now it is off to the command line! This will all be on the cloned drive. I am trimming out references to the other system drives for easy of reviewing.
If that actually did something I am not aware. Nothing additional seemed listed or mounted anywhere. I ran the below gpt commands, unmounted disk 4, and ran them again and checked Disk Utility/finder for any changes. Meanwhile assuming we are not actually mounting.
Same result for all /dev/disk* attempts
Seemed to result in no changes
both returned
Restart, option key at Chime = Clone drive does not appear
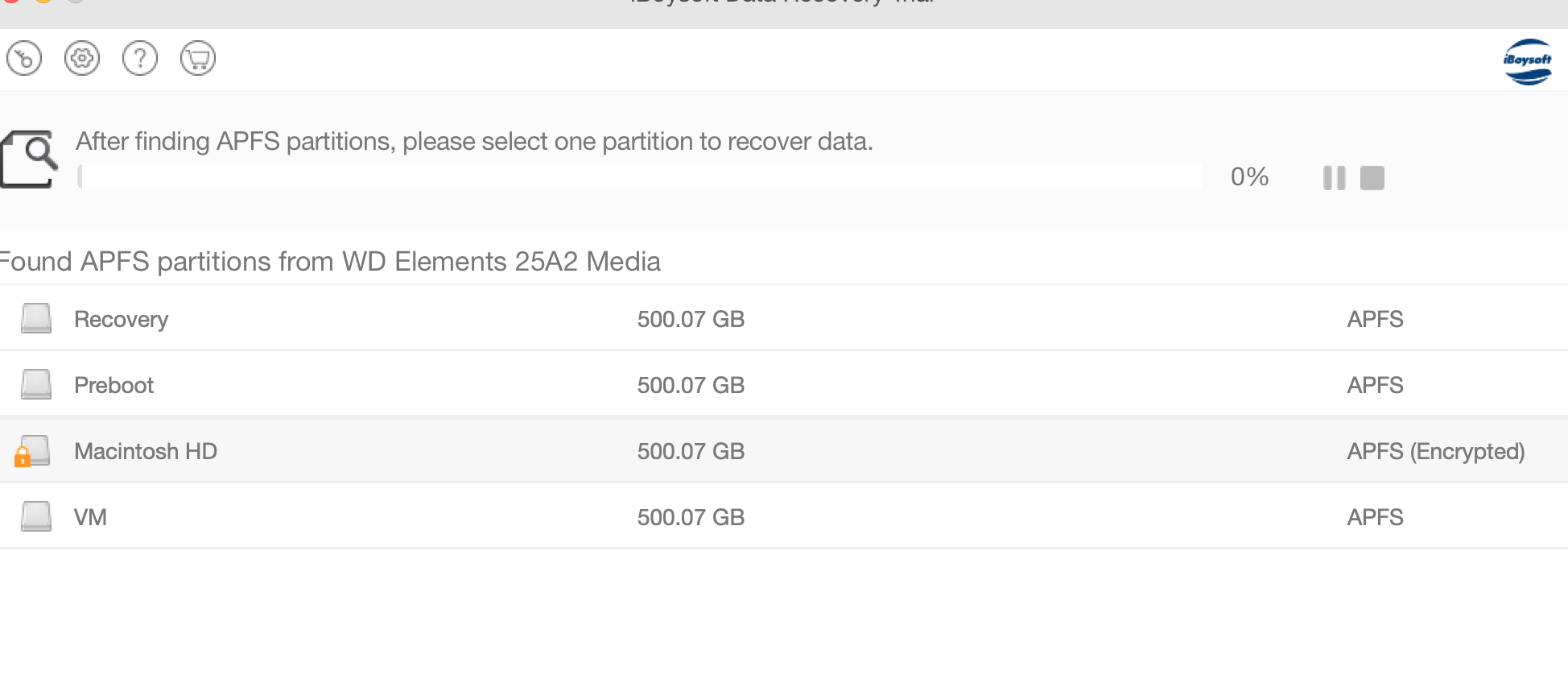
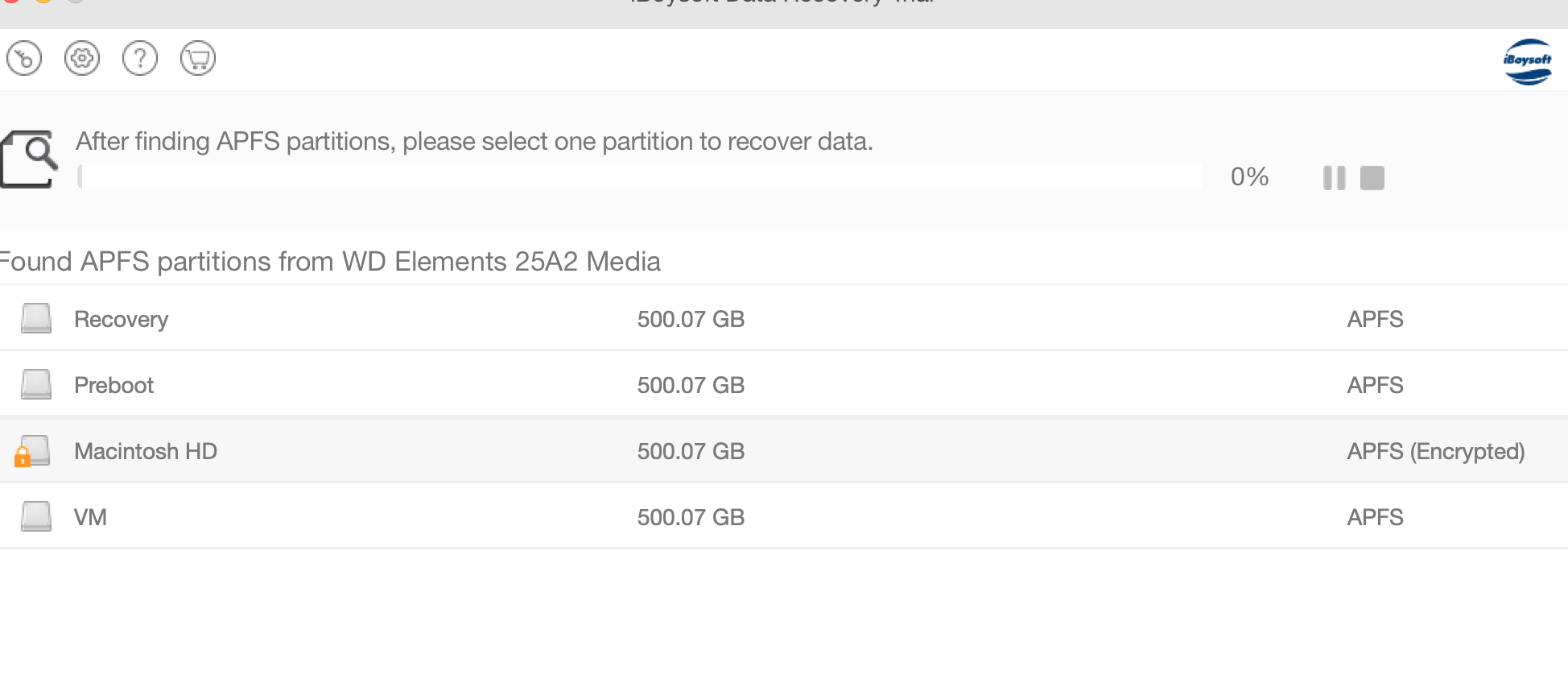
tried iBoysoft
iBoysoft sees it but does not accept the password and has no option to utilize recovery key (I did try this in addition to the password)
Tried Recovery Studio Pro on Win10 and it noted that no apfs keys were found after a full scan, which is why I am wondering if some item required to decrypt is wiped and if it might be able to be recovered and placed back in there from a backup.
I am just lost at what to do from here, or what may be missing. I assume getting the volume to show back up to where I can see it in terminal is the next step but I don’t know how to approach it.
Disclosure - after the above I did try some hail mary commands butI don’t mind recloning a fresh drive copy to try and work further on this.
Also worked with the that wouldn't mount using hdiutil but running out of characters here. Can recap if it may be helpful.
The set up, steps taken and how we got this far:
-Friend's 2015 Macbook Air stopped turning on. May have had a bad shutdown involved. Dead logic board.
-Drive Enclosure is obtained. The drive would not successfully boot into any macs at the Apple store. Genius Bar may or may not have run some commands to try and recover things. Report that part of the SSD that managed FileVault is probably damaged.
-Friend's university tech shop takes a look with no luck.
-They stress how important some of their research data is, I refer them to Drive Savers out of an abundance of caution.
-Drive Savers tries to hook it into a system (??), says it isn't working, sends them on their way within 15 minutes or so.
-Bottom line, the usual boot off of it on a different mac, etc troubleshooting isn't working.
-I take pity on them and have taken this on as a side project, believe this is an encrypted APFS drive.
-I manage to capture a seemingly 100% good 500GB disk image, and mirror to a 2TB external drive, directly off the bad drive in the enclosure on an Ubuntu system using ddrescue. For anyone else going through this with a drive that keeps dropping connection, try a powered USB hub.
ddrescue commands used
Code:
sudo ddrescue -f -n -c 4096 /dev/sdc "/media/spaceguns/TOSHIBA EXT/RescueImage1.dmg" "/media/spaceguns/TOSHIBA EXT/mapfile1.txt"
sudo ddrescue -d -f -r3 -c 4096 /dev/sdc "/media/spaceguns/TOSHIBA EXT/RescueImage1.dmg" "/media/spaceguns/TOSHIBA EXT/mapfile1.txt"
sudo ddrescue -d -f -r3 -c 4096 /dev/sdc /dev/sdb mapfile.txtNo bad sectors or errors on both, a quick look at the image in a hex editor and yep, stuff is in there alright. Have a backup of the dmg just in case.
Feeling a new level of confidence that I won't fry the last hope we have of getting this data back by hammering it with attempts, it's time to jump on my wife's Macbook Pro and see what we can see. Unfortunately, not being a mac guy, I am hitting some walls, probably caused by my own ignorance of the underlying system and available commands. I am comfortable at a command line, but I am not a mac user.
Mac Attempts and command results:
DISK UTILITY File>Open Disk Image>RescueImage1.dmg
Hangs and very briefly it appears on the left showing the following then it immediately disappears
Hooking the cloned drive up

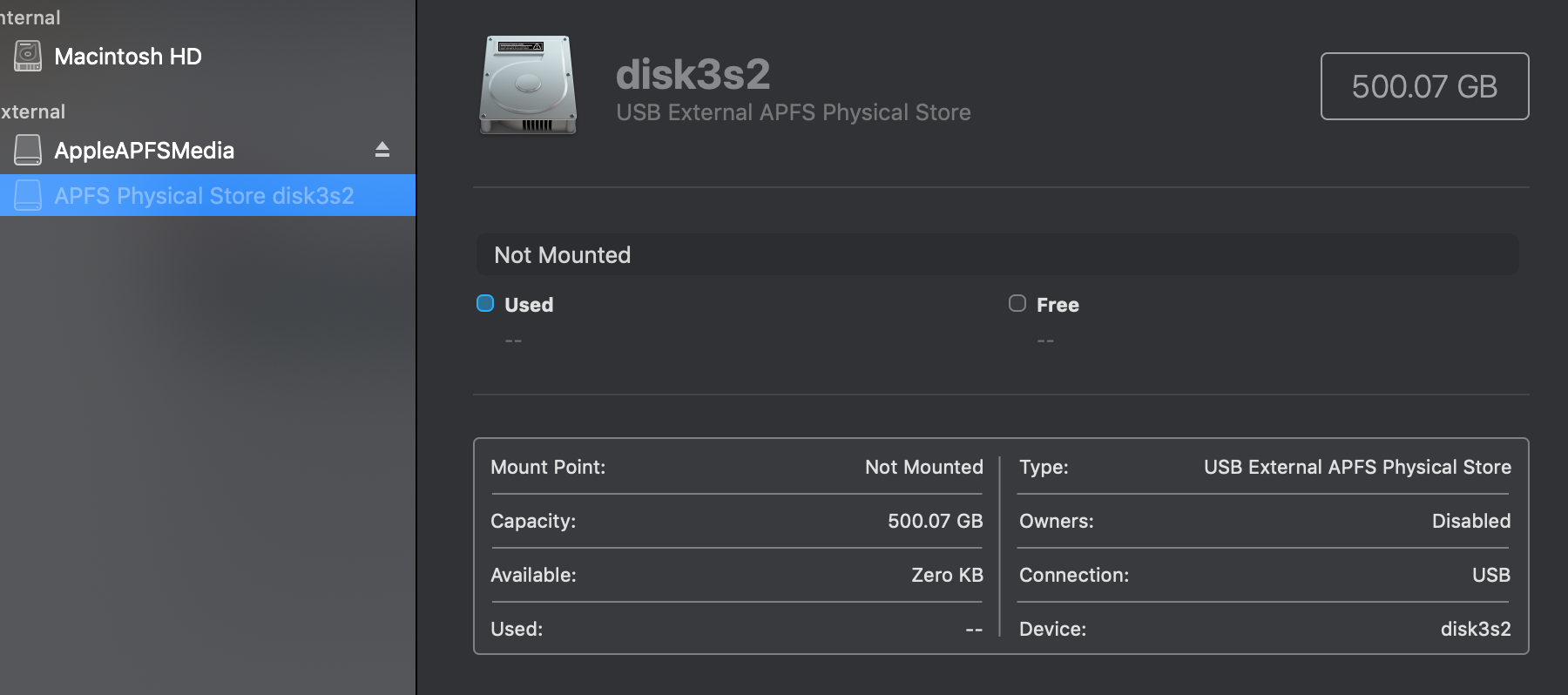
Click Mount on disk3s2 and nothing happens, no feedback
File->Get Info on disk3s2
Volume type : APFS Physical Store
BSD device node : disk3s2
Connection : USB
Device tree path : IODeviceTree:/PCI0@0/XHC1@14
Writable : No
Is case-sensitive : No
Volume capacity : 500,068,036,608
Owners enabled : No
Is encrypted : No
Can be verified : Yes
Can be repaired : Yes
Bootable : No
Journaled : No
Disk number : 3
Partition number : 2
Media name :
Media type : Generic
Ejectable : Yes
Solid state : No
S.M.A.R.T. status : Not Supported
Parent disks : disk3
File->Get Info on AppleAPFSMedia
Volume type : Uninitialized
BSD device node : disk4
Connection : USB
Device tree path : IODeviceTree:/PCI0@0/XHC1@14
Writable : No
Is case-sensitive : No
Volume capacity : 500,068,036,608
Available space (Purgeable + Free) : 0
Purgeable space : 0
Free space : 0
Used space : 500,068,036,608
Owners enabled : No
Is encrypted : No
Can be verified : No
Can be repaired : No
Bootable : No
Journaled : No
Disk number : 4
Media name : AppleAPFSMedia
Media type : Generic
Ejectable : Yes
Solid state : No
S.M.A.R.T. status : Not Supported
Disk Utility First Aid Results
Code:
Running First Aid on “AppleAPFSMedia” (disk4)
Fixing damaged partition map.
Invalid disk.
Operation failed…
Running First Aid on “” (disk3s2)
Repairing storage system
Performing fsck_apfs -y -x /dev/disk3s2
Checking the container superblock.
Storage system check exit code is 0.
Operation successful.Still no mount on disk3s2. I think I have exhausted my Disk Utility GUI options so now it is off to the command line! This will all be on the cloned drive. I am trimming out references to the other system drives for easy of reviewing.
Code:
Janes-MacBook-Pro:~ John$ diskutil list
/dev/disk3 (external, physical):
#: TYPE NAME SIZE IDENTIFIER
0: GUID_partition_scheme *2.0 TB disk3
1: EFI EFI 209.7 MB disk3s1
2: Apple_APFS Container disk4 500.1 GB disk3s2
/dev/disk4 (synthesized):
#: TYPE NAME SIZE IDENTIFIER
0: APFS Container Scheme - +ERROR disk4
Physical Store disk3s2
Janes-MacBook-Pro:~ John$ diskutil apfs list
APFS Containers (2 found)
|
+-- Container disk1 (trimmed data)
+-- Container ERROR -69808
======================
APFS Container Reference: disk4
Size (Capacity Ceiling): ERROR -69620
Capacity In Use By Volumes: ERROR -69620
Capacity Not Allocated: ERROR -69620
|
+-< Physical Store disk3s2 0804ED4C-B212-4BF2-B475-6026969AE826
| -----------------------------------------------------------
| APFS Physical Store Disk: disk3s2
| Size: 500068036608 B (500.1 GB)
|
+-> No Volumes
Janes-MacBook-Pro:~ John$ distill mountDisk /dev/disk3s2
One or more volume(s) failed to mount
Janes-MacBook-Pro:Documents John$ diskutil mountDisk disk4
Volume(s) mounted successfullyIf that actually did something I am not aware. Nothing additional seemed listed or mounted anywhere. I ran the below gpt commands, unmounted disk 4, and ran them again and checked Disk Utility/finder for any changes. Meanwhile assuming we are not actually mounting.
Code:
Janes-MacBook-Pro:~ John$ sudo gpt show disk3
start size index contents
0 1 PMBR
1 1 Pri GPT header
2 32 Pri GPT table
34 6
40 409600 1 GPT part - C12A7328-F81F-11D2-BA4B-00A0C93EC93B
409640 976695384 2 GPT part - 7C3457EF-0000-11AA-AA11-00306543ECAC
977105024 2929858399
3906963423 32 Sec GPT table
3906963455 1 Sec GPT header
Janes-MacBook-Pro:~ John$ sudo gpt show disk3s1
start size index contents
0 1 MBR
1 409599
Janes-MacBook-Pro:~ John$ sudo gpt show disk3s2
start size index contents
0 976695384
Janes-MacBook-Pro:~ John$ sudo gpt show disk4
start size index contents
0 122086923
Janes-MacBook-Pro:~ John$ diskutil apfs unlockVolume /dev/disk4
/dev/disk4 is not an APFS VolumeSame result for all /dev/disk* attempts
Code:
Janes-MacBook-Pro:~ John$ diskutil verifyVolume disk4
Started file system verification on disk4
Verifying storage system
Performing fsck_apfs -n -x /dev/disk3s2
Checking the container superblock
Storage system check exit code is 0
Finished file system verification on disk4Seemed to result in no changes
Code:
Janes-MacBook-Pro:~ John$ diskutil verifyDisk /dev/disk4
Janes-MacBook-Pro:~ John$ diskutil repairDisk /dev/disk4both returned
Code:
Unable to verify this whole disk: A GUID Partition Table (GPT) partitioning scheme is required (-69773)Restart, option key at Chime = Clone drive does not appear
tried iBoysoft
iBoysoft sees it but does not accept the password and has no option to utilize recovery key (I did try this in addition to the password)
Tried Recovery Studio Pro on Win10 and it noted that no apfs keys were found after a full scan, which is why I am wondering if some item required to decrypt is wiped and if it might be able to be recovered and placed back in there from a backup.
I am just lost at what to do from here, or what may be missing. I assume getting the volume to show back up to where I can see it in terminal is the next step but I don’t know how to approach it.
Disclosure - after the above I did try some hail mary commands butI don’t mind recloning a fresh drive copy to try and work further on this.
Also worked with the that wouldn't mount using hdiutil but running out of characters here. Can recap if it may be helpful.

